Programming Windows: Trustworthy (Premium)
- Paul Thurrott
- Jan 29, 2022
-
7
With the Windows XP launch behind it, Microsoft turned its attention to the future. This future was to include several Windows initiatives with 2002 deliverables, some public and some yet to be revealed.
Microsoft had promised to ship Windows XP Tablet PC Edition by the end of 2002, for example. But it was also prepping the next major release of Windows Server, then still called Windows .NET Server, and the first servicing update for Windows XP, called Windows XP Service Pack 1 (SP1). Longhorn development would speed through a set of “alpha” pre-release internal builds in 2002 before an external beta. Microsoft had yet another Windows XP variant, this one aimed at so-called Media Center PCs, that it would unveil at the Consumer Electronics Show (CES) in January 2002. And there were, of course, lesser releases aimed at vertical markets, like Windows XP Embedded and new variants of Windows CE, all of which would spread Windows XP’s NT-based DNA to new device categories.
Windows XP got off to a good start, given the industry doldrums and the post-911 uncertainties of the day. And it was well-reviewed, kicking off a new era for Microsoft’s most important, lucrative, and popular platform thanks to its solid and secure new foundations and consumer-friendly capabilities that were poised for a new era of connectivity.
But that new era unceremoniously came to a crashing halt less than two months after Windows XP shipped, and right in the middle of a well-deserved vacation for Jim Allchin, who had previously won the internal battle between Windows and the web and had successfully shepherded the back-to-back development of Windows 2000 and Windows XP. On December 20, 2001, the security researchers at eEye Security announced that they had discovered major security vulnerabilities in the recently released Windows XP.
“Windows XP, by default, ships with a UPNP (Universal Plug and Play) Service that can be used to detect and integrate with UPNP aware devices,” the firm explained. “eEye has discovered three vulnerabilities within Microsoft’s UPNP implementation: a remotely exploitable buffer overflow that allows an attacker gain System-level access to any default installation of Windows XP, a Denial of Service (DoS) attack, and a Distributed Denial of Service (DDoS) attack. eEye would like to stress the extreme seriousness of this vulnerability.”
UPnP is a technology that enables devices on a network to discover and communicate with each other seamlessly. The name is meant to evoke the earlier “Plug and Play” technology that Microsoft had created for Windows 95 and peripheral connectivity, especially via USB. Microsoft had added UPnP compatibility to previous Windows versions like Windows 98 and Windows ME, but it was disabled by default on those systems because of the relative rarity of home networking at the time.
Windows XP, however, was poised for a future in which home networks and connected devices would be common. And so UPnP was enabled by default. It was a decision Microsoft would quickly regret this decision, as it underscored its unsophisticated understanding of the security landscape. Microsoft’s critics in the security space were quick to jump all over the firm for this ineptitude. And Mr. Allchin’s vacation, alas, was cut short. He flew back to Redmond mid-trip, leaving family and friends behind, to face the music.
eEye, at least, had done the right thing: the security firm alerted Microsoft to the vulnerability and allowed Microsoft to issue a fix—via Security Bulletin MS01-059—before revealing it publicly.
“This is a serious vulnerability, and we strongly encourage customers to immediately apply the patch,” Microsoft noted. “An attacker who successfully exploited this vulnerability could change the UPnP subsystem to perform any desired task. Because the UPnP subsystem runs as part of the operating system, this would give the attacker complete control over the system … this vulnerability would enable an attacker to gain complete control over [all] of the computers on a [network] subnet … It’s very serious.”
Because of eEye’s disclosure, Windows XP’s UPnP vulnerability was never exploited. But the damage was done in the press: for all its impressive underpinnings, this new NT-based platform was easily subverted, and its frailty made headlines with mainstream news outlets. But its most vocal critics, of course, were more technical people in the security community.
“Who needs hackers?” security expert Richard Forno asked rhetorically, “we’ve got Microsoft! Windows XP was promoted by Microsoft as perhaps the ultimate and most secured Windows operating system the firm had ever created, and one of its key features was increased security from electronic evildoers like hackers, crackers, and so-called cyberterrorists … Unfortunately, Windows XP doesn’t protect you from Microsoft … Windows XP ships Universal Plug and Play (UPnP) enabled (turned on) by default … As a result of this oversight, someone could remotely use this feature to exploit, control, or disrupt a system from remote locations around the world.”
“Jim Allchin said that all buffer overflows were eliminated in Windows XP,” security expert Bruce Schneier added. “Not only was the UPnP vulnerability in Windows XP an unneeded feature that was enabled by default; it was a buffer overflow.”
Internally, Microsoft raced to find out what went wrong, and it found more than it had bargained for. Everywhere it looked, it seemed, it found more and more Windows source code that would not withstand the new connected era that Microsoft was championing. And it wasn’t just Windows: with one major exception, the .NET Framework, Microsoft had been shipping insecure code without formal review processes.
In January 2002, Microsoft chairman and chief software architect Bill Gates emailed a “call to action” to the firm’s 50,000 employees. Microsoft, he said, had a new highest priority: it must build a “Trustworthy Computing” environment for customers that would be as reliable as the electricity that powers their homes and businesses. And the infrastructure that would enable this trustworthiness, go figure, was .NET.
“No Trustworthy Computing platform exists today,” he told employees. “It is only in the context of the basic redesign we have done around .NET that we can achieve this. The key design decisions we made around .NET include the advances we need to deliver on this vision. Visual Studio .NET is the first multi-language tool that is optimized for the creation of secure code, so it is a key foundation element.”
Key aspects of his Trustworthy Computing initiative should include availability, security, and privacy, Gates said. And Microsoft would need to completely change the way it developed software in order to keep its customers’ trust at every level. He briefly mentioned a “downtime” that might occur as Microsoft shifted to address this new imperative. Microsoft’s software, going forward, would be “secure by default.”
In an interesting coincidence, the .NET team had just undergone a 6-week security review ahead of a planned February launch of the first version of the .NET Framework. That team had formalized the notion of measuring or scoring a product’s “attack surface,” and instead of seeking to eliminate all security bugs, which was considered impossible, it promoted reducing that attack service as much as possible. And so Microsoft’s senior leadership directed the Windows team to undergo a similar security push for the next Windows deliverable, Windows .NET Server, before its release later that year.
It didn’t go well. As the server version of Windows XP and the basis for future XP versions, Windows .NET Server consisted of roughly ten times the source code as .NET, and that codebase included reams of legacy code, some dating back over 10 years. Likewise, the Windows engineering staff was over five times the size of the .NET organization, and all 8,000 of them would need to be trained in security principles. That worked started in January, right after the Gates menu.
This work was beyond distracting, and it is not coincidental that Microsoft had little to say about Windows XP in the first quarter of 2002 despite this biggest-ever Windows version having just shipped. At CES in early January, Bill Gates had shown off two Windows-related initiatives, Mira and Freestyle, that would extend Windows XP to wireless smart displays and a coming generation of Media Center PCs, respectively. But that was about it until several months later. In the interim, Microsoft discovered so many security problems during its code reviews that it halted work on new code company-wide.
“Quality always adds to profit,” Microsoft CEO Steve Ballmer explained of the “hold” on new development. “It doesn’t hurt it. Does it really hurt you to delay a product for a month, two months, three months? If your customers are a lot happier, they’re much more inclined to buy it. They are more inclined to deploy if you don’t have so many support costs behind it. I don’t think it hurts our bottom line. I think it’s entirely consistent with our bottom line.”
In February, Microsoft revealed that it planned to deliver Windows XP Service Pack 1 (SP1) in the second half of 2002. SP1, which was in development before Trustworthy Computing, would consist of a “roll-up of critical updates, enabling technologies for ‘Mira’ and new types of PCs like the Tablet PC and Media Center PCs, and the changes required by Microsoft’s consent decree with the DOJ and the nine states.” A source at Microsoft told me that the first beta was expected in May with the final release that August.
Internally, however, Microsoft was preparing a much bigger update than SP1: it would instead deliver a future version of Windows XP that included all the security work it was doing in Windows .NET Server, but that release—which might be a second Windows XP service pack or a so-called “second edition”—wouldn’t arrive until the following year. There were rumors about this release throughout 2002, with much speculation on how it would impact the Longhorn schedule.
After a successful Windows Hardware Engineering (WinHEC) event in April—more on that soon—Windows XP was back in the news. Microsoft had sold over 32 million copies of the new platform in just six months, making it one of the fastest-selling versions of Windows yet. “This quarter Windows XP shipped on nearly 60 percent of all new PCs, which represents a faster penetration than any of our previous operating systems,” Mr. Allchin said at the time. One wonders why that wasn’t even higher.
Windows XP SP1 entered public beta in June. Microsoft told me that it was “in most ways a traditional service pack,” meaning that it would include security fixes, application compatibility updates, and updated drivers.” But “included in the security updates will be fixes developed during the security push done by the entire Windows division as part of Microsoft’s renewed emphasis on security for customers,” plus the changes required by its consent decree.
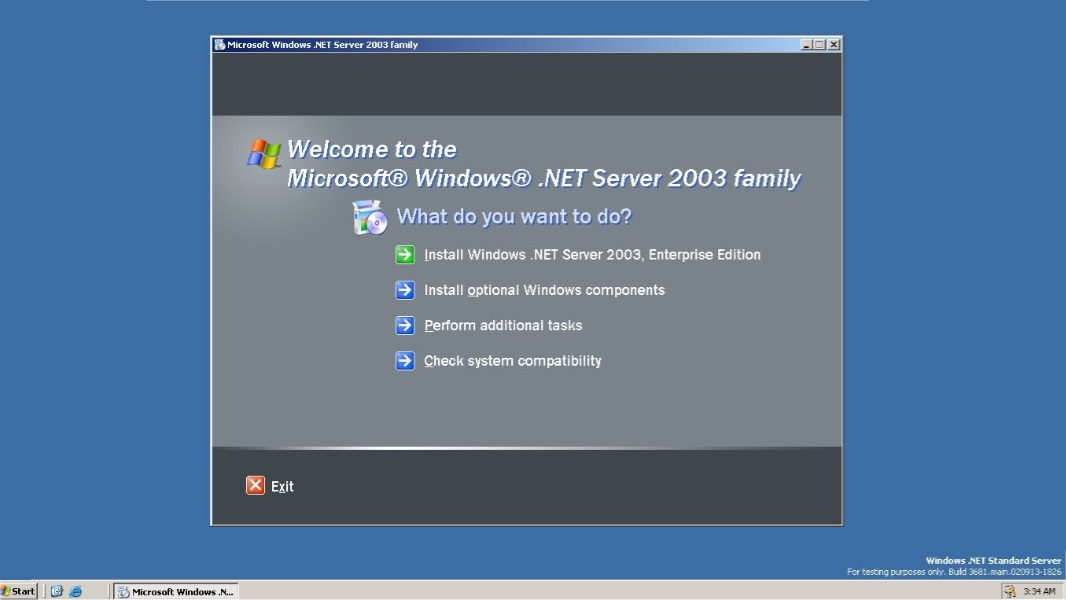
At a June reviewer’s workshop for Windows .NET Server Family near Microsoft’s Redmond headquarters, Microsoft promised a late 2002 release. It was a bewilderingly complex series of products spanning several product editions and dozens or perhaps even hundreds of new functional capabilities. Most important to this discussion, it would be the first Microsoft product to ship in the wake of the Trustworthy Computing code reviews. “Windows .NET Server is secure by design, secure by default, and secure in deployment,” Microsoft’s Bill Veghte told us.
It would include “a significantly reduced attack surface,” we were told, with a secure VPN gateway, a new secure wireless standard called 802.1x, and a standards-based TCP/IP infrastructure, including support for DNS, DHCP, NAT, and IPv6. Its IIS 6 web server would not be enabled by default, and Microsoft had disabled 20 other services by default, when compared to Windows 2000. The firm also reduced the privileges for some services, including NetworkService and LocalService. There were stronger Access Control Lists (ACLs, pronounced “ackles”) and policy default settings, and blank password attacks were eliminated because no network authentication was provided for accounts with blank passwords.
Locking down IIS and other services was eye-opening, the company said.
“The first thing we discovered when we locked down the server was that no applications worked,” Microsoft’s Brian Valentine explained. “They needed IIS or whatever. It was definitely a compatibility issue. But we learned a lot by locking down the server. Our general vision—the focus on general-purpose computing OSes—is deployment-specific. As you install it, you can choose the mode you want to run in, and we will configure it for you as well as we can. But we want it to be secure by default, and if you mess with something, you should be told about it: ‘This is the risk. This is the exposure you are taking.’ The system will get that knowledgeable, but the couplings between system behaviors need to be tightened up first.”
But Microsoft wasn’t done pushing security. In July, it announced yet another security initiative, codenamed Palladium, that would use an unnamed hardware component—a “new security computing chip”—in future PCs to give users “greater data security, personal privacy, and system integrity … The fundamental benefits of Palladium fall into three chief categories: greater system integrity, superior personal privacy, and enhanced data security.” It would require changes to the Windows kernel and create a new trustworthy execution subsystem within Windows.
“Palladium will greatly reduce the risk of many viruses and spyware—software that captures and reports information from inside your PC—and other attacks,” Microsoft general manager John Manferdelli explained at the time. “Memory in Palladium PCs and other devices will run only ‘trusted’ code that is physically isolated, protected, and inaccessible to the rest of the system. Files within the Palladium architecture will be encrypted with secret coding specific to each PC, making them useless if stolen or surreptitiously copied.” But it wouldn’t arrive until at least 2004 in “a future version of Windows.”
As the summer of 2002 wound down, Microsoft announced that Windows .NET Server would be renamed … to Windows .NET Server 2003. And by then, it had done the work needed to ensure that this product didn’t succumb to the same avoidable security flaws that had plagued Windows XP.
“Engineered for security,” Windows .NET Server 2003 underwent another round of internal security code reviews, with the team ultimately concluding that its work had been successful, and that “Windows Server 2003 was on track to set a new standard for Microsoft operating system security.” That said, they also discovered new classes of vulnerabilities—subsequently fixed before its public release—and found further areas to improve security.
Key among these changes was Internet Explorer (IE), Microsoft’s web browser. Declaring that it was “a server not a surfboard,” Microsoft locked down IE in Windows .NET Server 2003, preventing most of the obvious underlying vulnerabilities. These changes would delay the release of the product past the end of 2002, with its launch—as Windows Server 2003, with no .NET branding—finally taking place in April 2003. But bigger changes to IE and Microsoft’s general security posture were coming, however, to both .NET Server 2003 and Windows XP via future service packs.
Looking back on Windows XP’s security nightmares, Jim Allchin would later observe, “where security is concerned, lunch is expensive. If you don’t pay for it now, you’ll pay an order of magnitude more for it later. Pay now or pay later: it comes down to the way you develop your code.”
Gain unlimited access to Premium articles.
With technology shaping our everyday lives, how could we not dig deeper?
Thurrott Premium delivers an honest and thorough perspective about the technologies we use and rely on everyday. Discover deeper content as a Premium member.