Online Accounts 2025: Migrating to Proton Authenticator (Premium)
- Paul Thurrott
- Jul 31, 2025
-
18

It’s been a big year for Little Tech. But there’s no company in this space that I trust more than Proton, so I was delighted that it announced Proton Authenticator, a 2FA app that works on all desktop and mobile platforms. As a Proton fan and a daily user of the Proton Pass password manager, I naturally set out to install and configure Proton Authenticator immediately, starting with my phones. And I am not surprised to say that I quickly moved to see whether I could replace the two authenticator apps I had been using with this solution.
That raises some questions, I know. So let me start with those.
? What is 2FA? And what is an authenticator app?
Most are at least passingly familiar with password managers, which should be called identity managers because they hold the key to much more than just our online accounts. If not, please check out Password Management Basics (Premium) for a refresher. 2FA is an additional layer of protection for your online accounts. The most common 2FA methods are email- and text message based, where you try to sign in to an online account, and it prompts you to provide this additional layer of protection by checking your email or texts to get a 6-digit code that you then enter as well. But it’s more secure to use a dedicated authenticator app for 2FA codes. These apps are typically on your smartphone.
Good password managers offer two-factor authentication, or 2FA, capabilities in addition to whatever else they do. So it’s possible to use a single app, your password manager, to autofill your username and password when you try to sign-in online and then use the app again to obtain a 2FA code when prompted. However you do it, app-based authentication is more convenient than email-based authentication, and it’s more secure than text-based authentication. Passkeys, which are also supported by good password managers, are even more secure and even more convenient, but they’re also less common. And so all of us will have some mix of authenticator app and passkey capabilities across the various accounts we access on PCs, phones, and other devices.
Consider a typical scenario. You open a web browser, desktop or mobile, and navigate to some website for which you have an account. If you’ve never signed in on this device, or perhaps if some time frame has transpired, the site will prompt you to enter your credentials, typically a username and password.
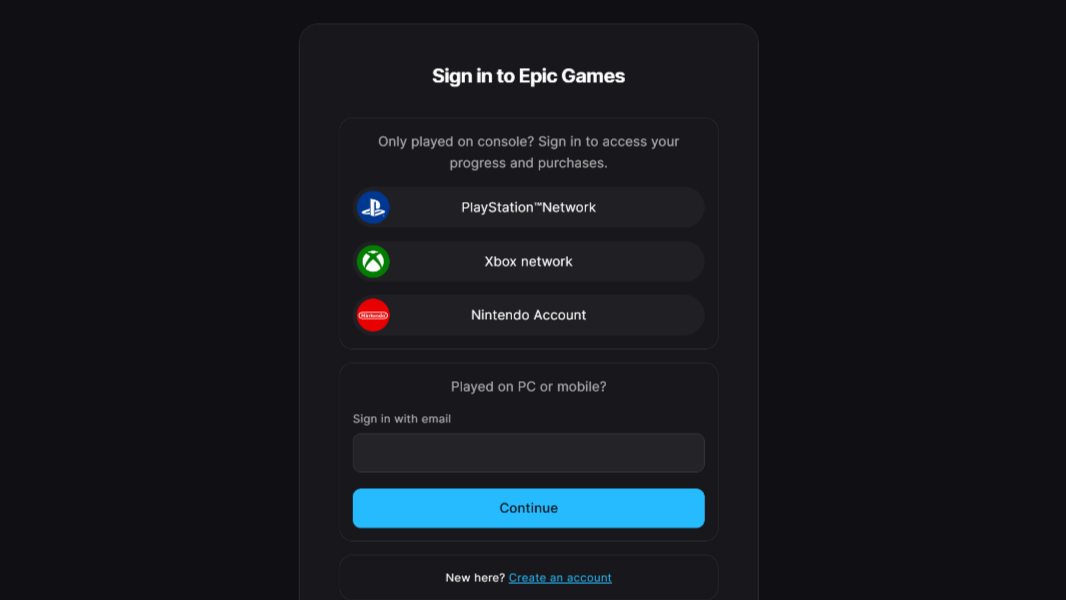
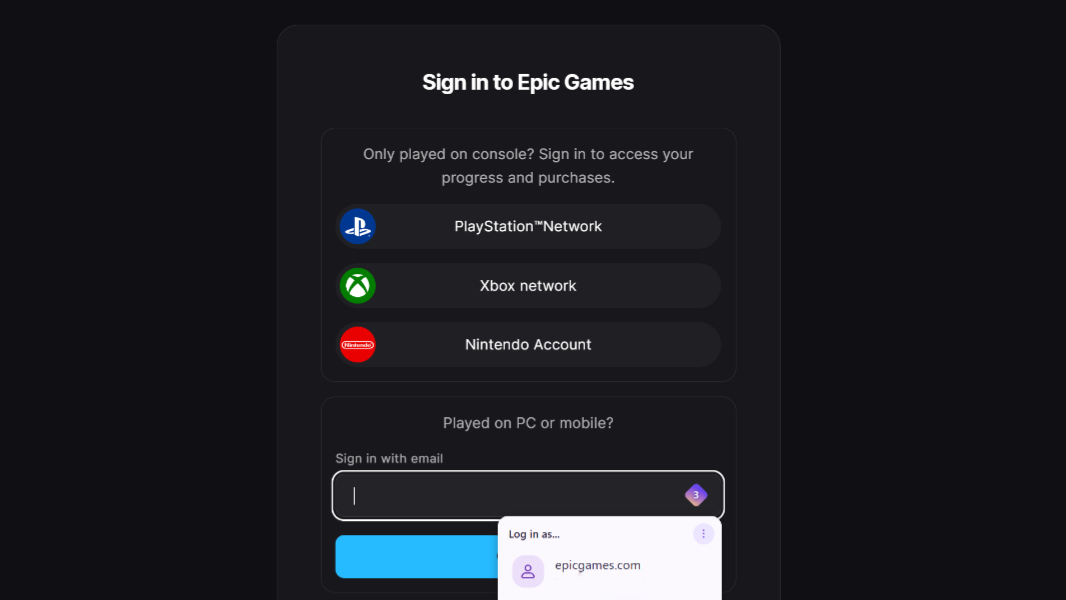
If you’ve configured a password manager browser extension (desktop) or app (mobile), it will appear automatically to autofill these credentials.
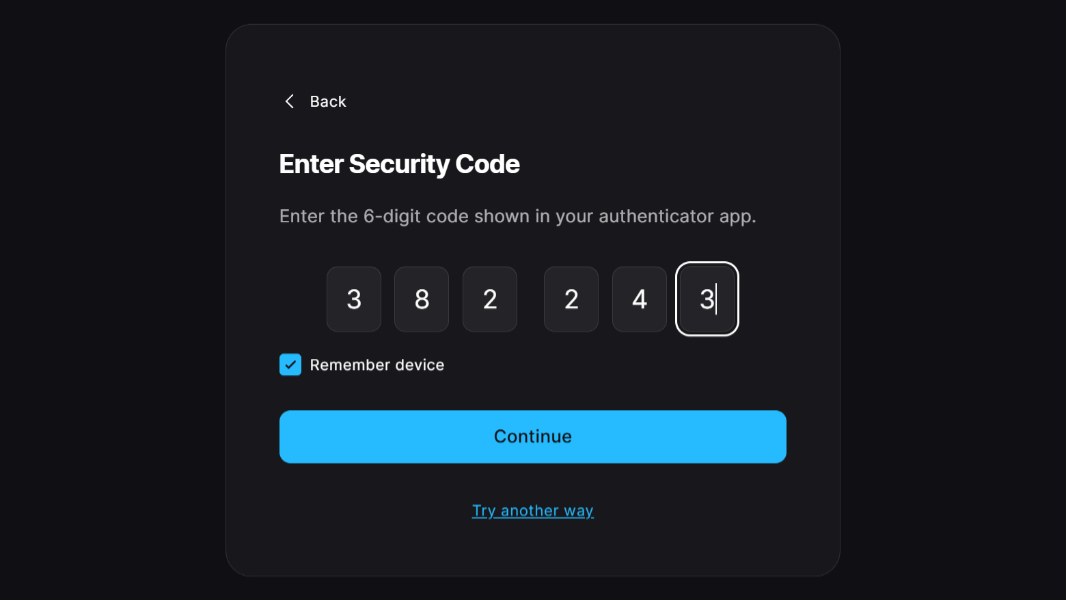
And if you’ve configured the account to require 2FA with an app, you’ll be prompted to enter a code to complete the sign-in.
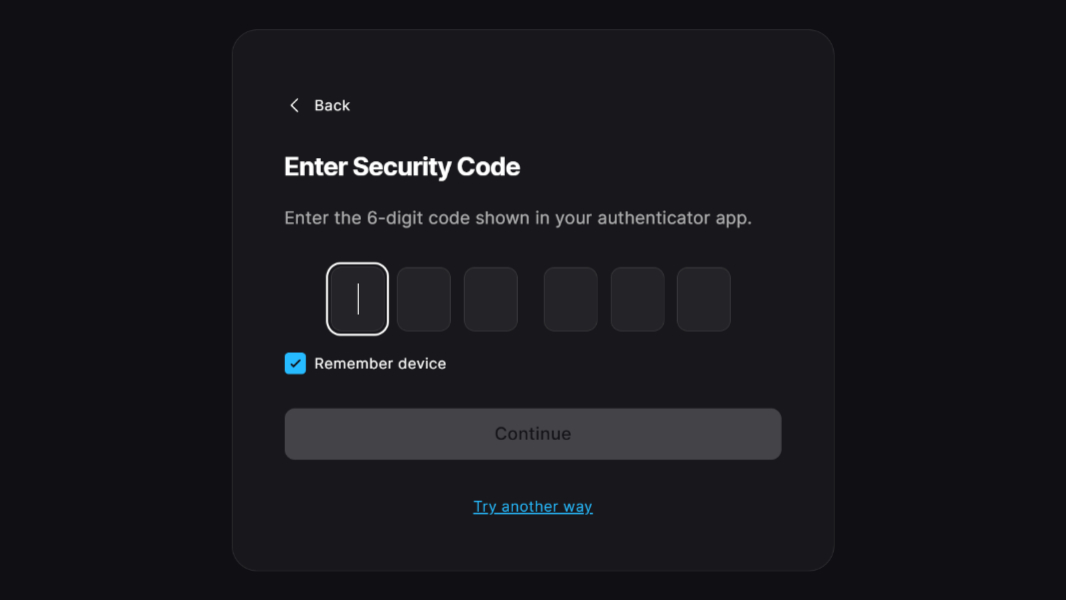
You get this code from your authenticator app or password manager. That app will require you to authenticate first, ideally using biometrics (facial or fingerprint recognition). And then you locate the account in the list of accounts, where you will find a time-limited six-digit code. If you’re doing this on the same device (typically your phone), you can just tap the code to put it in the clipboard, and then paste that into the security code field back in the web browser. If you’re signing in on a PC or other computer, you can just look at the code on the phone and type it into the field on the computer.
I recommend–and use–configuring separate password manager and authenticator apps. And many accounts support multiple 2FA methods, in which case I recommend using an authenticator app first and then email as a backup.
Why?
Security experts will tell you that separating the username/password combinations stored by password managers from the security codes stored by a standalone authenticator app is just common sense. You don’t store the key for a vault in that vault, after all. But I will tell you that security is an eternal battle between convenience and efficacy, and that we all have our own choices to make. In my case, I choose to be more secure with authentication (2FA) codes. But I’m also a hypocrite in that I use my password manager, Proton Pass, to store both usernames/passwords and passkeys. And … yeah. ]\
Confusing matters, I was also using two 2FA authenticator apps, Google Authenticator and Microsoft Authenticator. And therein lies a story.
2️⃣ Why was I using Google Authenticator and Microsoft Authenticator?
Proton Authenticator is a direct replacement for Google Authenticator. It does everything that app does, plus it adds end-to-end synchronization for cross-device sync. This is a classic security compromise in the sense that the convenience of that sync (albeit without true E2E sync with Google) outweighed what I perceived to be a minor security downgrade. But with Proton, there’s no compromise.
Microsoft Authenticator is much like Google Authenticator, but with one limitation. It can’t sync your account codes through the cloud so that they are available on whatever devices you use with this app. And I really like that feature. Rely on it, really. (Microsoft does offer a backup feature, at least.)
Proton Authenticator can also replace Microsoft Authenticator, but the one thing it doesn’t replicate is a sort of unique capability that Microsoft created for its online accounts. That is, instead of prompting you for a code, Microsoft’s online accounts will trigger its Authenticator app to prompt you in different ways, such as matching the number you see wherever you’re trying to sign-in with one of three numbers the app displays on your phone.
To my knowledge, this is unique to Microsoft. And so I’d been using both Google Authenticator and Microsoft Authenticator. The latter only for my Microsoft accounts (consumer and commercial) and the former for everything else. This worked fine because I never needed to manually find and launch Microsoft Authenticator. Every time I needed to authenticate, it would notify me on my phones, so I could make it happen.
I may end up sticking to this configuration, but substituting Google with Proton Authenticator. For the short term, I’ll test when using Microsoft accounts with Proton makes sense. This is easier for me than most, since I test so many laptops and write a book about Windows 11, for which I use a consumer Microsoft account (MSA). But I’ll still need a few weeks of testing to be sure. And, of course, the first thing I had to do was get this going across my various phones and, perhaps, my PCs and iPad too.
So I started with Google Authenticator.
?♂️ Migrating from Google Authenticator
The Proton Authenticator migration experience varies by app, with apps that offer a direct way of exporting data offering the best experience. Google Authenticator is such as an app. All I had to do was open the app, navigate to Menu (≡) > Transfer accounts, and choose “Export accounts.” By default, all the accounts were selected, which is what I wanted, and then Google generated three QR codes, which I could page through.
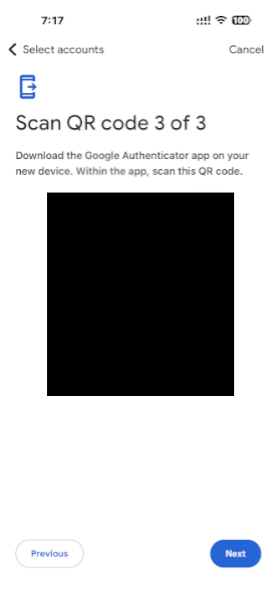
If I were doing this on two devices, I could have scanned those codes, one-by-one, in Proton Authenticator on a second device to important whatever number of accounts each contained. But I was doing this on a single device, and so I took a screenshot of each QR code instead. Once I got past that, I was prompted to remove the exported accounts, which is smart. But I waited on that to make sure they imported correctly first.
In Proton Authenticator, you can import accounts during initial set up, as prompted, or you can do it later via an Add account (“+”) button on the home screen, as with other authenticator apps. This presents a camera view (after enabling camera permissions) so you can scan a QR code, by default, with an “Enter manually” option and a Camera roll-type icon on the bottom. I chose the latter, and that let me scan the code from each screenshot in turn. Which worked fine.
?♀️ Migrating from Microsoft Authenticator
Migrating from Microsoft Authenticator proved more difficult. This app doesn’t support an export option, and it’s one of two authenticator apps marked with a yellow bang in Proton Authenticator’s “Import codes” interface (the other is Authy), indicating that there is no export available. I was told to contact Microsoft to suggest this feature. And that I would need to manually import my data for now.
No problem. I do have several Microsoft accounts (MSAs), but only one of them is a primary account, and I only configure four in Microsoft Authenticator. I’ve gone through the process of adding an MSA to an authenticator app so many times, it’s almost second nature. So I knew it would be easy, and just a little time consuming.
And that was true for three of those accounts, including my primary account, thankfully. But the fourth account, which I use for the Windows 11 Field Guide, was configured in an odd way in the Microsoft Authenticator app, with only an auto-generated one-time password code but no way to authenticate a passwordless sign-in request. For some reason.
I won’t bother anyone with the details, since this has nothing to do with Proton Authenticator, but it did take me almost 30 minutes to fix this problem, which involved resetting the account’s password and multiple failed attempts at signing in via whatever combinations of private browser windows, PCs, and phones. But I finally figured it out, and I did get that account configured correctly with Proton Authenticator.
But if you do use Microsoft Authenticator with numerous accounts, migrating to any other authenticator app will be a bit of a slog.
? Proton Authenticator on other phones
I installed and configured Proton Authenticator on my iPhone first, and then I later did so on my Pixel and Samsung Android phones. But there are some differences.
With the iPhone, you can back up Proton Authenticator to iCloud, which will help if you use this app on a Mac and/or iPad too. But there’s nothing like that on Android, of course. Curious, I clicked into “Backup” on the Pixel and found a single option, “Automatic backups.” When I enabled that, I had to give permission for a notification that would tell me each time the data was backed up. And then I had to pick a location in the phone’s file system to store the backup. Hm.
That’s not great, and common file locations like Downloads can’t be used for semi-obvious reasons. If I could have used my Synology Drive, I would have, but it was just the local phone file system. And so I backed out and enabled “Sync between devices” and, after signing in with my Proton account as required, “Biometric” sign-ins. When I did that, all the account codes from my iPhone appeared, replicated on the Pixel. This happened later on the Samsung Galaxy S25+ as well. Which is what I wanted, as this is the way it works on Google Authenticator, though Proton’s solution is a bit more secure.
?️ Proton Authenticator on desktop?
I use Proton Authenticator on my Windows PCs, but almost always just in the web browsers I use, and not via a standalone app. So I was curious what that might look like with Proton Authenticator. (I had installed Microsoft Authenticator and Google Authenticator on my iPad, too, and so I will do that with Proton Authenticator as well.)
Well, this shouldn’t be have been surprising to me or you, but it’s just like the mobile app. You download and install it, run it, and when you select “Sync between devices,” you’re prompted to sign-in to Proton, and then all the account codes appear. I also enabled the “Biometrics” app lock, which uses Windows Hello, of course.
The only big difference is visual: Thanks to the PC’s bigger and wider screen, you get two or more columns of account codes instead of just one on the phones. I assume iPad works similarly, but I will try that later.

(The automatic backup option in Windows also prompts you to back up to the file system. I did not enable this, but here I could back up to Synology or some cloud storage system since they’re all accessible from the file system.)
?️ Proton for the win
Proton Authenticator and Proton Pass are an unbeatable combination, and for all the right reasons. It’s Proton, so they’re both secure and easy to use. Both apps are available everywhere. And both apps sync between all your devices seamlessly. Perfect.
The import functionality works great with supported authenticator apps like Google Authenticator. But it’s not Proton’s fault that some apps, like Microsoft’s, don’t support this feature. This is like any other Big Tech blocker, in which you have a one-time task to undergo so that you can be rid of this silliness and dig your way out of the moat that Microsoft, in this case, erected.
The one potential pitfall here, and this may be true for many of you, is whether it may make more sense to stick with Microsoft Authenticator for our Microsoft online accounts. I will keep testing this and see how it goes. But since I was already using Google Authenticator for non-Microsoft accounts, wherever I land is still better than the previous situation: One more step away from untrusted Big Tech companies that couldn’t care less about their individual customers and one more step closer to the more trusted embrace of Little Tech companies like Proton. Which is the best of the lot.
More soon.
Gain unlimited access to Premium articles.
With technology shaping our everyday lives, how could we not dig deeper?
Thurrott Premium delivers an honest and thorough perspective about the technologies we use and rely on everyday. Discover deeper content as a Premium member.