Microsoft Account Goes Passwordless
- Paul Thurrott
- Sep 15, 2021
-
26
Anyone with a Microsoft account can now remove their password from the account entirely to enable better security.
“For the past couple of years we’ve been saying that the future is passwordless, and today I am excited to announce the next step in that vision,” Microsoft corporate vice president Vasu Jakkal writes in the announcement post. “Beginning today, you can now completely remove the password from your Microsoft account.”
As for the “why” of this change, Microsoft points to the fact that passwords are insecure and are the focus of over 18 billion attacks every year, or 579 attacks every second.
Before you can go passwordless, you’ll need the Microsoft Authenticator app on your smartphone. Then, you can use Windows Hello, a security key, or a verification code that’s sent to an email address, your phone, or a compatible app or service like Outlook, OneDrive, Microsoft Family Safety, and more to sign-in, depending on the location.
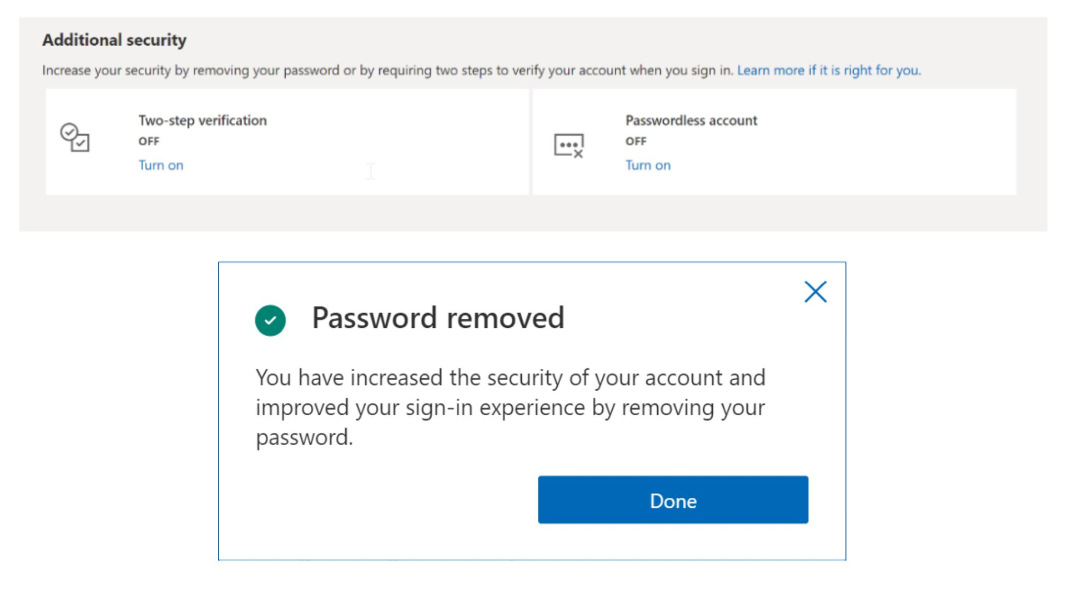
To get started, you will need to sign-in to your Microsoft account on the web and enable the option “Passwordless account.” Then, just follow the on-screen prompts and approve the change from your Microsoft Authenticator app. (You can always re-add a password to the account later if you prefer.)
This capability is now available on consumer-oriented Microsoft accounts. Microsoft previously made passwordless sign-in a feature of its commercial Microsoft 365 accounts as well. You can learn more about going passwordless from the Microsoft website.