Chrome Mobile Susceptible to Phishing Attacks
- Paul Thurrott
- Apr 29, 2019
-
5
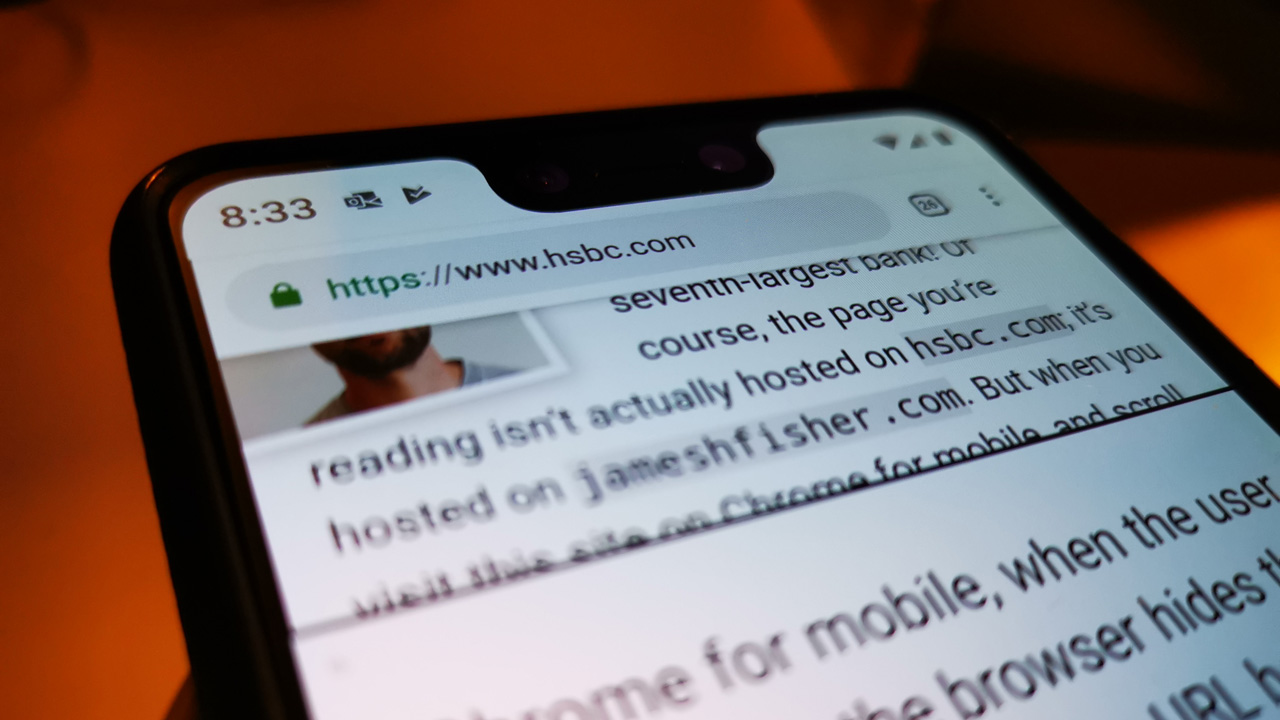
A software developer has identified a simple exploit in the mobile version of Google Chrome that can be used for phishing attacks. He calls it “the inception bar.”
“In Chrome for mobile, when the user scrolls down, the browser hides the URL bar and hands the URL bar’s screen space to the web page,” developer James Fisher explains. “Because the user associates this screen space with ‘trustworthy browser UI,’ a phishing site can then use it to pose as a different site, by displaying its own fake URL bar – the inception bar!”
As Mr. Fisher explains it, that behavior is bad enough. But thanks to the programmable nature of Chrome mobile, hackers could also trick the browser into never re-displaying the real address bar, which typically happens if the user scrolls back up the page or scrolls to the top of the page.
That behavior explains Fisher’s name for the hack: In the movie Inception, characters could be robbed while dreaming. “Like a dream in Inception, the user believes they’re in their own browser, but they’re actually in a browser within their browser,” he explains. “The user thinks they’re scrolling up in the page, but in fact, they’re only scrolling up in the scroll jail [in which the real address bar is never displayed].”
In case it’s not obvious, a fake address bar could be styled to look like a secure website for a bank or other service, and fool users to enter private data like user names and passwords. Fisher says he’s not sure how a user could protect themselves from this flaw, and he views it, correctly, as a security flaw in Chrome mobile.
Google has not yet publicly commented on this issue. And, yes, I assume the new Chromium-based Edge is susceptible to this type of attack as well.