The Secret Lives of Passkeys (Premium)
- Paul Thurrott
- Dec 27, 2023
-
6

While 2023 was the year of AI hype, it was also the year in which passkeys were broadly adopted by online services and users alike. This technology is finally making the post-password world a reality, and that’s true no matter which platforms and ecosystems you prefer and use. It’s the democratization of the passwordless dream.
I love that. But for us here in the Microsoft sphere, there’s also a paradox inherent to passkeys. On the one hand, no company has done more to implement passwordless technologies at scale than Microsoft—it first allowed Microsoft account (MSA) holder to remove the password from their accounts over two years ago, for example. But on the other, Microsoft has been curiously silent this past year or so while Amazon, Google, and the rest of Big Tech tripped over themselves and each other, promoting their adoption of passkeys incessantly.
By comparison, Microsoft was as quiet as the proverbial church mouse. It mentioned passkey management support in Windows 11 version 23H2 in passing, preferring to market that release’s unpolished Copilot functionality above all else. And then GitHub, which many don’t even associate with Microsoft, made its passkey implementation generally available around the same time. But that was about it, and you’d be forgiven for not noticing either milestone.
But passkeys have been on my radar all year. And as I started organizing the 23H2-related updates I’d be making to the Windows 11 Field Guide, I decided early on that they would include a new chapter about passkeys, knowing full well that writing such a thing would require a lot of work, experimentation, and new writing. And that’s exactly what happened. To paraphrase J.R.R. Tolkien, who famously noted that the tale grew in the telling, the writing, um, grew in the writing. Which is an awkward way to communicate that one thing led to another, and I suddenly found myself writing several thousand additional words more than expected. This is a big topic, and it seemed that every time I made a conceptual breakthrough, there was more to explore and then more to explain.
But I think I can bring this home for you in a way you will enjoy, assuming you’re a long-time Microsoft follower. Because as it turns out, Microsoft began the work that led to passwordless generally and passkeys specifically well over two decades ago when it announced that it was working on the awkwardly-named Next Generation Secure Computing Base (NGSCB) as a hybrid hardware and software implementation of its Trustworthy Computing ideals. Among this system’s many security advances was the notion of securely authenticating our digital identities—what we today call online accounts—using something we know (a password or PIN), something we have (a smartcard or phone), and something about us (a fingerprint or eye).
NGSCB led to the creation and standardization of the Trusted Platform Module (TPM) security chip and the many hardware-based security innovations it enables in Windows. But it also led indirectly to what we would now call Microsoft account integration in Windows and then more directly to the account sign-in options that first arrived in Windows 8, PIN and Picture password. Then, Microsoft formally implemented an end-to-end passwordless sign-in for Microsoft accounts (and all password-protected accounts) in Windows 10 called Windows Hello that stores your account credentials in the PC’s TPM, securing its PIN- and facial and fingerprint recognition-based sign-in options and passing them through to apps and websites.
Windows 11 carries forward with this system, but it also tellingly requires a more capable and secure TPM 2.0 chipset and requires users to enable at least a Windows Hello PIN when they sign in to the system with a Microsoft account (or any other account that’s protected with a password, by default. And this is the part of the story when I get to reveal a little secret that I suspect most readers are unaware of: When you use Windows Hello PIN, facial, or fingerprint recognition to sign in to your Microsoft account, you are actually using a passkey. Put another way, Microsoft’s NGSCB initiative of 20+ years ago was all about getting us to this exact moment in time.
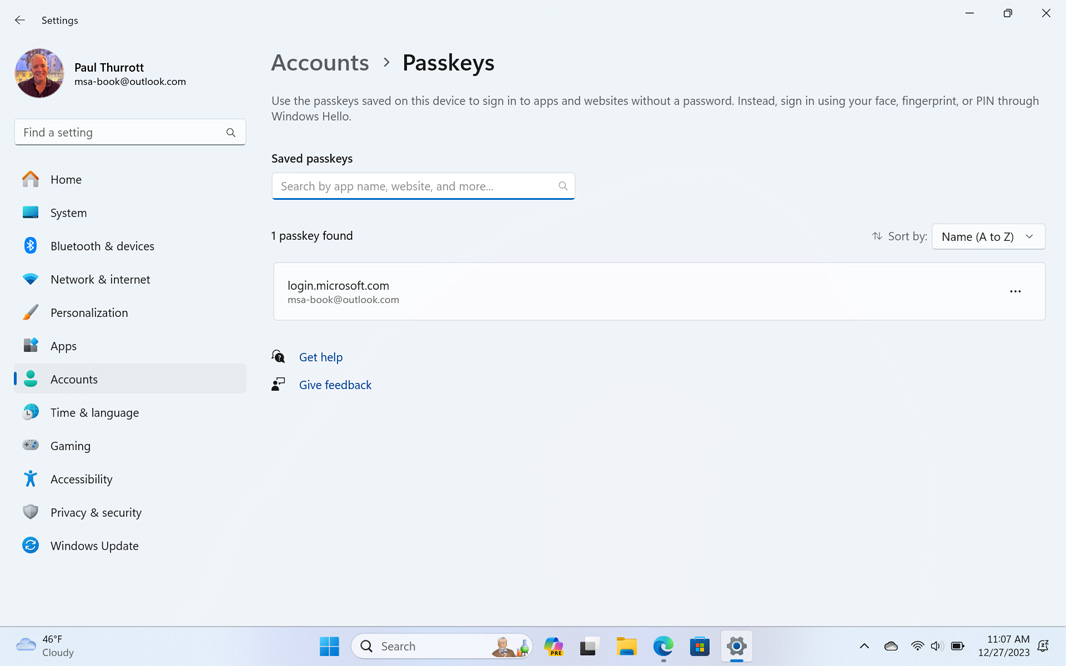
This isn’t conjecture. As noted, Windows 11 version 23H2 includes native passkey management capabilities via a very simple interface in the Settings app. And as soon as you sign in to your MSA on a freshly set up PC, you can open Settings, navigate to Accounts > Passkey settings, and see that there is a single passkey already configured on that PC. It’s for your sign-in account. And because it’s for your sign-in account, all you can do here is look at it, not delete it. That is, you can’t “manage” it.
It is this passkey, stored in your TPM’s encrypted storage, that enables the authentication pass-through capabilities that make Windows 11 what it is today. It’s why you can sign in automatically to services like OneDrive and Outlook.com, to the in-box apps, and to the websites and online services you access with Microsoft Edge. This end-to-end ecosystem is driven entirely by a single passkey on the PC.
Because this is so seamless, you have to go out of your way to see it working. Here’s one way: Open a web browser you’ve not signed in to yet, or perhaps an Edge InPrivate window, and begin signing in to your MSA at a Microsoft website like OneDrive or Outlook.com. After you’ve entered your email address and clicked “Next,” you’ll be prompted to authenticate yourself according to how your sign-in account is configured. For example, if you enabled two-factor verification as I recommend in Tip: Properly Secure Your Microsoft Account, it will default to sending a notification to your phone.
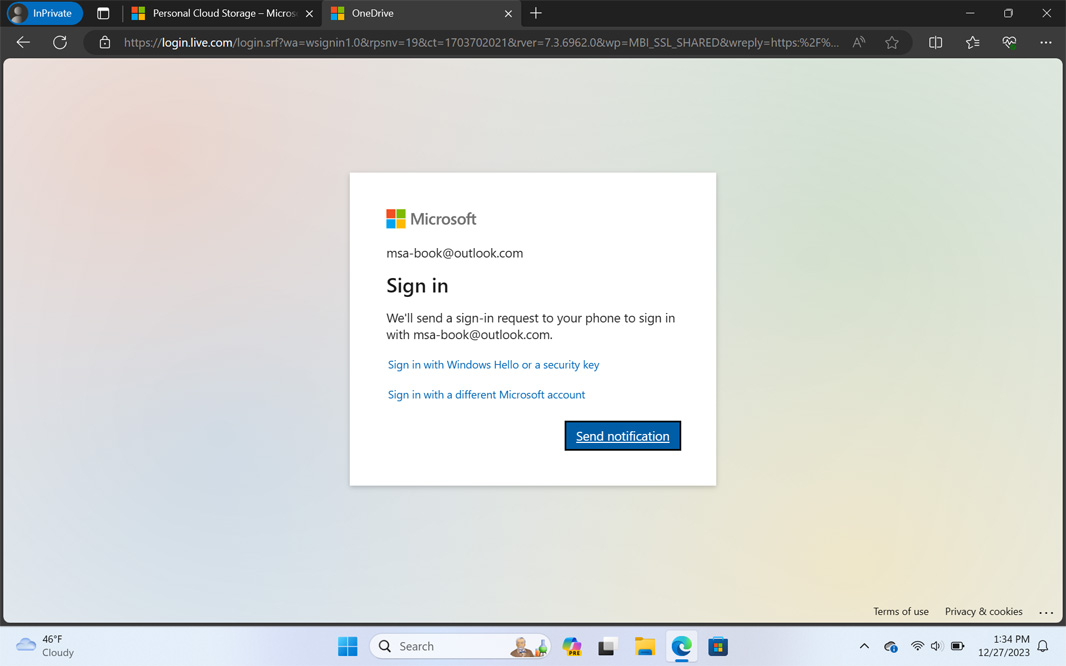
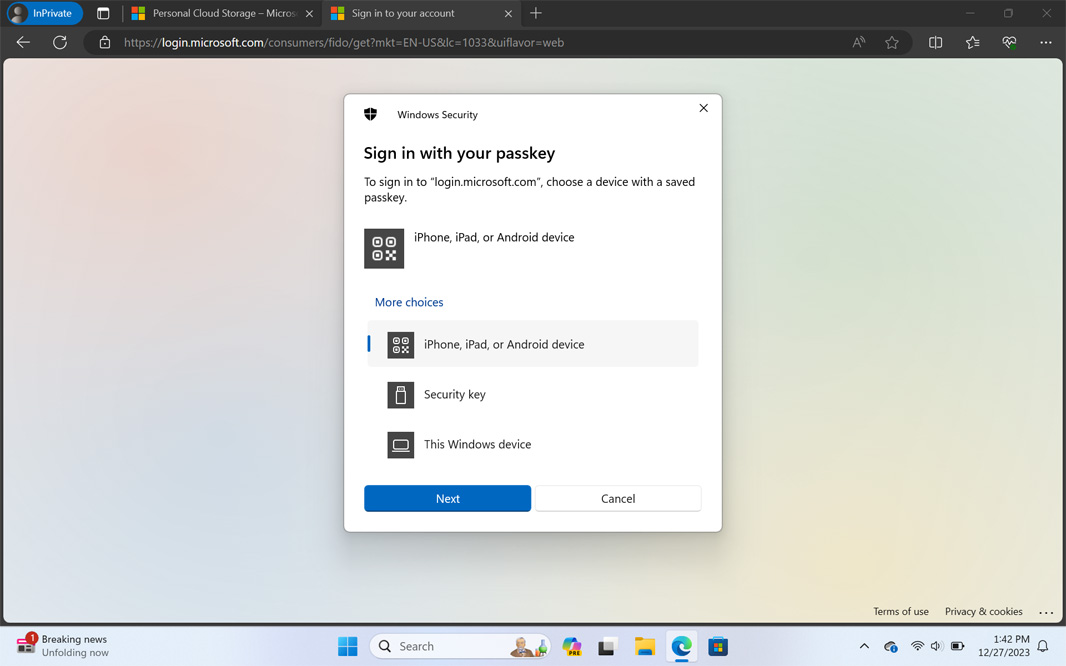
But notice those other options. Instead of clicking “Send notification,” you can also choose to “Sign in with Windows Hello or a security key.” Both of those options are a passkey. Windows Hello is the passkey that was saved in your PC’s TPM chip when you created the Windows sign-in, and the security key is a physical fob that has a passkey saved in its own encrypted storage (assuming you configured one for your MSA, as I have). The only difference between the two is that the Windows Hello option is only accessible on this PC, while the security key is portable, so the passkey(s) it contains can be accessed from any PC or portable device. (In that way, a security key is much like your phone-based Microsoft Authenticator app.)
When you click “Sign in with Windows Hello or a security key,” the system will prompt you to authenticate with whatever Windows Hello sign-in type you have used most recently. (In this case, I’ve only configured a PIN.)
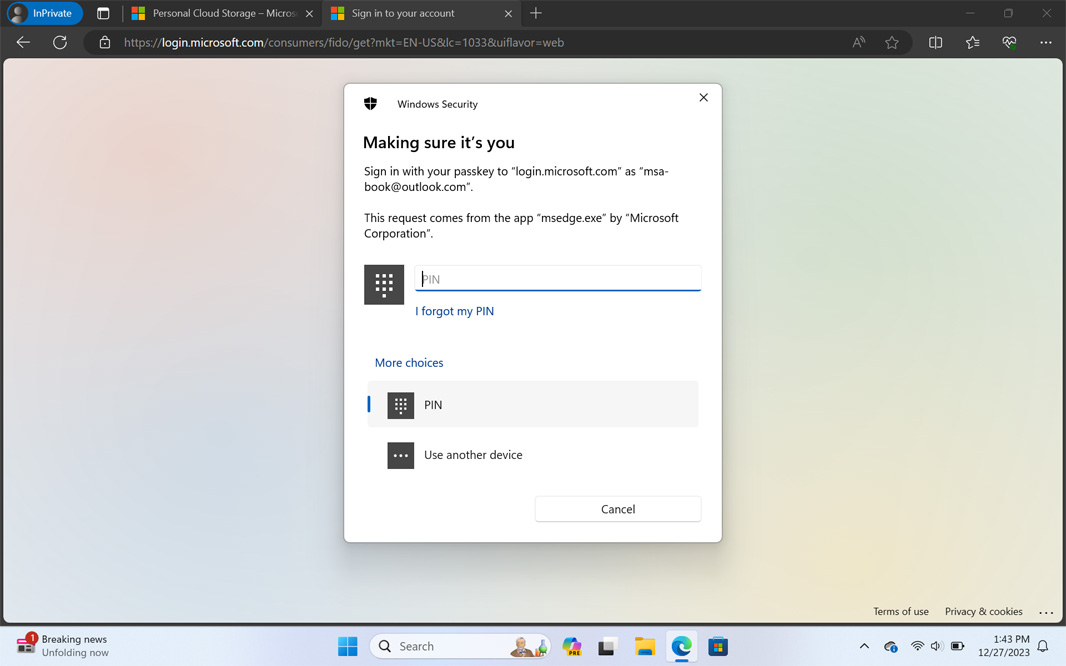
But you can also access other choices, Windows Hello facial or fingerprint recognition, if configured, or “Use another device,” which lets you access a passkey you may have stored on a smartphone or security key. Passkeys are everywhere now.
(And if you did enable two-factor verification as I recommended in that earlier post, you will be prompted to authenticate again, using a different additional sign-in or verification method the first time you do this. That’s the point of two-factor verification, but you’ll only have to do this one time.)
So, yes, the new passkey “management” functionality in Windows 11 version 23H2 is pretty lame. But it’s also just a side effect of the culmination of a 20+ year journey to bring passwordless to the masses. Given this, I’m surprised Microsoft hasn’t trumpeted its successes more publicly, because in this case, the successes of its competitors are its successes too. From the beginning, it knew that the NGSCB initiative would require industry-wide adoption and thus would need to be based on open standards, not proprietary Microsoft technologies. It knew it needed the help of chipset makers, PC makers, and software and services creators to make it happen. And as the world evolved, as web and mobile shifted our usage away from just PCs, it needed these ideas to be implemented and evolved by others as well. And that’s exactly what happened.
So, yes, enjoy using passkeys on your iPhone, Macs, and Android phones. Smile to yourself every time you seamlessly sign in to your Amazon or Gmail account without ever having to remember or type the password. But remember how all this started, which company laid the groundwork and showed the way with its own implementations. And even though it seems vaguely embarrassed to take credit, so much so that it doesn’t even really use the term passkey in the UI where it should do so, remember this was all Microsoft’s doing. So, yeah. They lost mobile, I get it. And they aren’t really dominant in any meaningful way on the web, especially with consumers. But our lives are all better today thanks to the broad adoption of passkeys, and it’s going to get even better in 2024.
So, here’s something I don’t get to say that enough.
Thanks, Microsoft.
Gain unlimited access to Premium articles.
With technology shaping our everyday lives, how could we not dig deeper?
Thurrott Premium delivers an honest and thorough perspective about the technologies we use and rely on everyday. Discover deeper content as a Premium member.