Microsoft Authenticator Gains Password Management and Autofill Capabilities
- Paul Thurrott
- Dec 15, 2020
-
40
Microsoft Authenticator can now provide password management and autofill capabilities on mobile, so you can protect synced passwords with multi-factor authentication (MFA), and using the Microsoft account you trust. This capability is now available in public preview.
“Microsoft Authenticator can now securely store and autofill passwords on apps and sites you visit on your mobile device,” Microsoft’s Rajat Luthra writes in the announcement post. “Once you make Authenticator an autofill provider, it will offer to save your passwords when you enter them on a site or app’s login page. Your passwords are protected on mobile with multi-factor authentication [and] are synced using your Microsoft account (outlook.com, hotmail.com, live.com, etc.), making them also available on your desktop with Microsoft Edge and [Google Chrome using a] new Chrome extension.”
To date, Microsoft Authenticator has provided MFA capabilities for your Microsoft, Azure Active Directory (AAD), and other compatible accounts. But this new capability dramatically expands the functionality of the app, letting you also sync all of your passwords more securely through your Microsoft account on mobile. That is, you can now replace the default password management and autofill capabilities on your phone with Microsoft Authenticator.
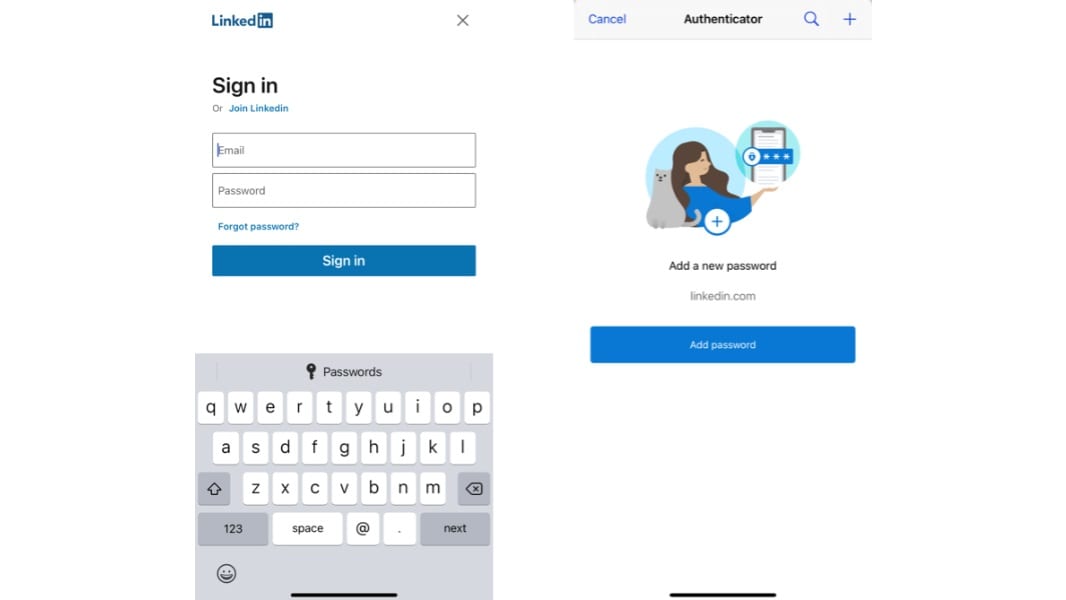
To get started, update Microsoft Authenticator to the latest version and then navigate to Settings > Beta > Autofill and enable this feature. A new Passwords tab will appear in the main app view alongside the previous tab, now called Authenticator.
Then, you need to configure Authenticator as your autofill provider. On iPhone, open Settings, search for “Autofill Passwords,” and then select “Autofill Passwords” and then “Authenticator.” On Android, open Settings, search for “Autofill,” and then select “Auto-fill service,” “Auto-fill service,” and then “Authenticator.”
These passwords will automatically sync with Microsoft Edge on desktop. If you’re using Google Chrome despite all common sense, then you can install the Microsoft Autofill extension to gain this ability.
A couple of more important points.
Microsoft Authenticator only supports password management and sync through a Microsoft account. You cannot use this feature with a commercial (AAD-type) account; admins interested in enabling autofill through the Microsoft Authenticator app for their organization can refer to the Microsoft Docs website.
Microsoft Authenticator password management and sync also requires iOS 12.0 or newer or Android 6.0 or newer.