Microsoft, Please Address the Recall Concerns Immediately (Premium)
- Paul Thurrott
- Jun 03, 2024
-
8
In what can only be described as the most avoidable PR nightmare in recent Microsoft history, the withering criticism of Windows 11 Recall continues unabated. This is an issue Microsoft should have predicted and countered with thorough documentation proving its security and privacy claims.
But this isn’t just on Microsoft: From the BBC to every Microsoft hater on the planet, the claims that Recall is easily hacked are easy to debunk, and range from basic scare tactics to outright misinformation. I’ve already made the case that Windows 11 Recall isn’t a privacy concern. And nothing written since then to the contrary has proven otherwise.
And yet here we are.
Let’s frame this discussion properly. Any argument about Recall that starts with an individual needing to sign in to the PC in question with admin privileges, in-person or remotely, can be ignored. This is a basic security issue that has nothing to do with Recall in many ways, but if a PC is so insecure that such a thing is possible, there are more immediate concerns.
I spent most of last December documenting how one can and should correctly secure their Microsoft account (MSA), and a big part of why you should do so is that you can sign in to your Windows PC securely. And that requires a PIN, at minimum–this policy is enabled by default in Windows 11–but more ideally a more secure Windows Hello biometric authentication type, like facial or fingerprint recognition.
If you do these things–secure your MSA, sign in to Windows 11 with that MSA, and enable Windows Hello–you’re secure. Your sign-in is secure, and the PC’s disk will automatically be encrypted. Together, these things ensure that someone else with physical access to the PC, like a thief, can’t sign in to your account and can’t remove the PC’s storage or otherwise read its contents. This is the baseline.
But Copilot+ PCs, the only PCs that can use Recall, are even more secure than that because they introduce further security requirements into this chain of protection. This is described below, but this simple fact negates any issues raised by those who got Recall working on non-Copilot+ PC hardware: Those systems are not secured as well as Copilot+ PCs, rendering those discussions moot.
Tied to this, I would like you to think–really think– about what it is these people are complaining about. To “prove” that Recall is insecure, they have ripped the application/service out of software code, enabled it on insecure, non-compliant PCs using local admin access, and then claimed they’ve found some soft underbelly. Now think about who Recall is for: Normal people who will buy a new PC, review this option, enable it if desired, and then use it on a PC that’s secure. People who will never hack Recall to make it work on non-compliant hardware. This whole conversation is idiotic.
OK. So, what makes a Copilot+ PC more secure?
Copilot+ PCs have a Microsoft Pluton security processor, which is an advance over the basic TPM security chip found in most modern PCs. And they utilize a new authentication technology called Windows Hello Enhanced Sign-In, which is enabled by default. No one attempting to prove Recall is insecure is using this exact combination of security controls on their PCs, thus whatever arguments they make can be ignored: These things–a secured MSA sign-in, automatic disk encryption, a Pluton security processor, and Windows Hello Enhanced Sign-In–are what together secure Recall specifically and a Copilot+ PC generally.
So what’s Windows Hello Enhanced Sign-In? According to Microsoft Learn, it “provides an additional level of security to biometric data by leveraging specialized hardware and software components, such as Virtualization Based Security (VBS) and Trusted Platform Module 2.0 to isolate and protect a user’s authentication data and secure the channel by which that data is communicated.”
Do you think that each of the people desperately trying to prove that Recall is insecure have all these protections enabled? Or do you think that they are just hacking Recall to prove their point?
That’s rhetorical. None of them have–or even can–meet that bar. They are all doing the latter, and in doing so, they are misrepresenting–purposefully or not–the truth. They are lying and they are wasting our time. Among other things, “Enhanced Sign-in Security is only supported on devices configured by a device manufacturer to enable the capability.” Copilot+ PCs are among those devices. And they are not available publicly.
Now, there will come a day when Copilot+ PCs are available. And it may pass that someone discovers a security or privacy issue with this feature that doesn’t require another person to access the PC physically or remotely with admin privileges. And on that day, we will have a different discussion. That discussion will include facts like this feature is still in preview, and for a reason, and you need to opt in to it during initial Setup, and there are so few Copilot+ PCs out in the world right now that the impact is very low, and so on. And so we’ll see.
But for now, given where we are in time and what we know about how Copilot+ PCs will be secured, and what the requirements are before you can even access Recall legally/normally, nothing has changed. Window Recall is not a privacy (or security) concern. Not yet.
But other people, other publications, prefer to get hits no matter the consequences. And so you will see articles like this one from The Verge that present easily disproven claims in a headline and thus subvert the role of journalism. Yes, a security research does claim that Recall is a security “disaster,” but no, he is not correct, and for all the reasons noted above. A better headline, a more credible report, would tell the truth: We don’t know yet.
Here’s the Medium blog post that The Verge story links to. And here’s how it starts: “I got ahold [sic] of the Copilot+ [PC] software and got it working on a system without an NPU.”
Ah.
Well, then nothing you write after that sentence matters. For all the reasons noted above.
Again, this researcher and others may very well find that a properly configured and secured Copilot+ PC exhibits some or even all the vulnerabilities he claims exist. But that hasn’t happened. He literally had to hack Recall onto a non-Copilot+ PC, negating every concern and claim.
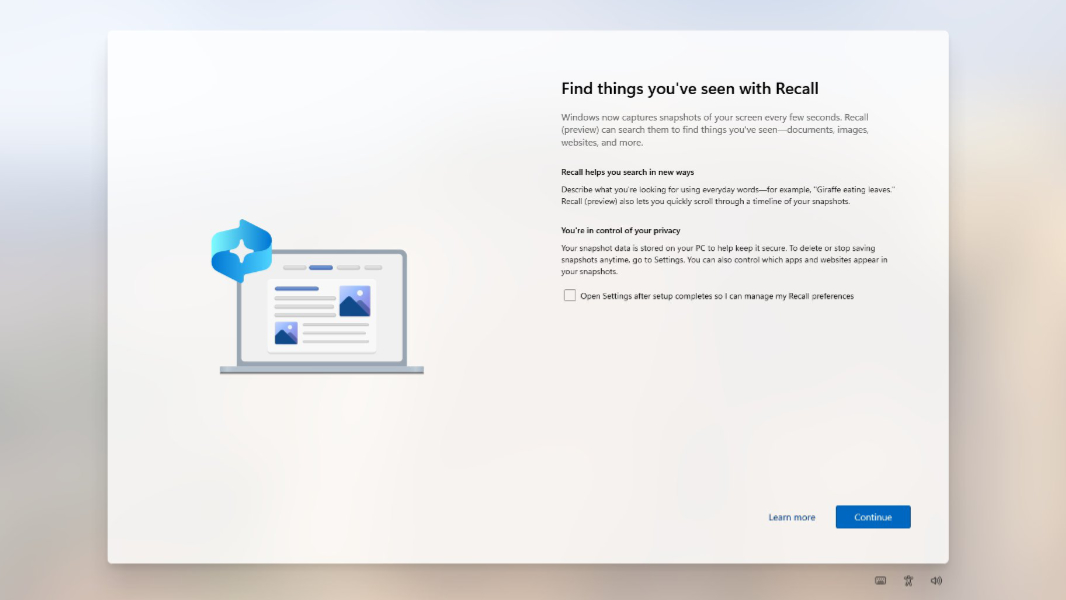
If I have one complaint about Recall–and, to be clear, this too needs to be tested against shipping Copilot+ PC hardware–it’s that the option to “opt-in” during initial Setup is the same kind of dark pattern language Microsoft uses elsewhere. To be fair to Microsoft, that’s partially less problematic because the PC is fully secured before you even see this screen. But this is still not OK: There should be an On/Off switch, and Recall should literally be disabled by default.
But again. Even that complaint is qualified by the obvious: Like everyone else on earth, including that security researcher, I do not yet have a real Copilot+ PC. So my opinion is just that.
Gain unlimited access to Premium articles.
With technology shaping our everyday lives, how could we not dig deeper?
Thurrott Premium delivers an honest and thorough perspective about the technologies we use and rely on everyday. Discover deeper content as a Premium member.