25H2 Feature Focus: Administrator Protection (Premium)
- Paul Thurrott
- Aug 26, 2025
-
5

Windows 11 version 25H2 will ship with a major security advance called Administrator Protection. Depending on how you use the PC, it could be disruptive.
❓ Why?
It’s not worth going through the entire convoluted history of user accounts in Windows, but the big milestones there are Windows NT, the transition to the NT code base for mainstream users in Windows XP, User Account Control (UAC), which debuted in Windows Vista, and then the ability to sign in to Windows using an online account, beginning with Windows 8.
Along the way, PCs became more secure with Trusted Platform Module (TPM) security chips, biometric authentication via Windows Hello, and then end-to-end security guarantees with the Copilot+ PC platform and Windows Hello Enhanced Sign-In Security (ESS).
Through all this, the advice to individuals has remained largely unchanged: Though the first account you create on a Windows PC will always be an administrator account with its associated elevated privileges, you should always create a second account with standard user privileges and use that account day-to-day.
Also largely unchanged over those decades: Almost no one does that.
Microsoft has tried all kinds of things to combat the risks associated with signing in to Windows with an admin account. UAC is perhaps the most obvious because it was initially so disruptive, but initiatives like the Metro/Modern app platform and S mode should also be viewed as part of this work. And Microsoft also took many smaller steps to basically protect users from themselves.
But none of it worked. And as the Secure Future Initiative (SFI) begat the Windows Resiliency Initiative, Microsoft introduced a coming Windows 11 feature that might actually solve the problem. It’s called Administrator Protection.
? Why not just improve UAC?
We’ve been using UAC for so long now that many of us probably forget about the problem that it tried to solve: Previous to Windows Vista, all apps and services that ran while an admin user was signed in ran with (elevated) administrator privileges. With UAC, most apps and some services run with standard user privileges even if the signed-in user is an admin. And apps are given a virtualized copies of the file system and registry. If an app or service requires elevation, the user is shown a UAC prompt that appears modally over the rest of the desktop in a special Secure Desktop mode.
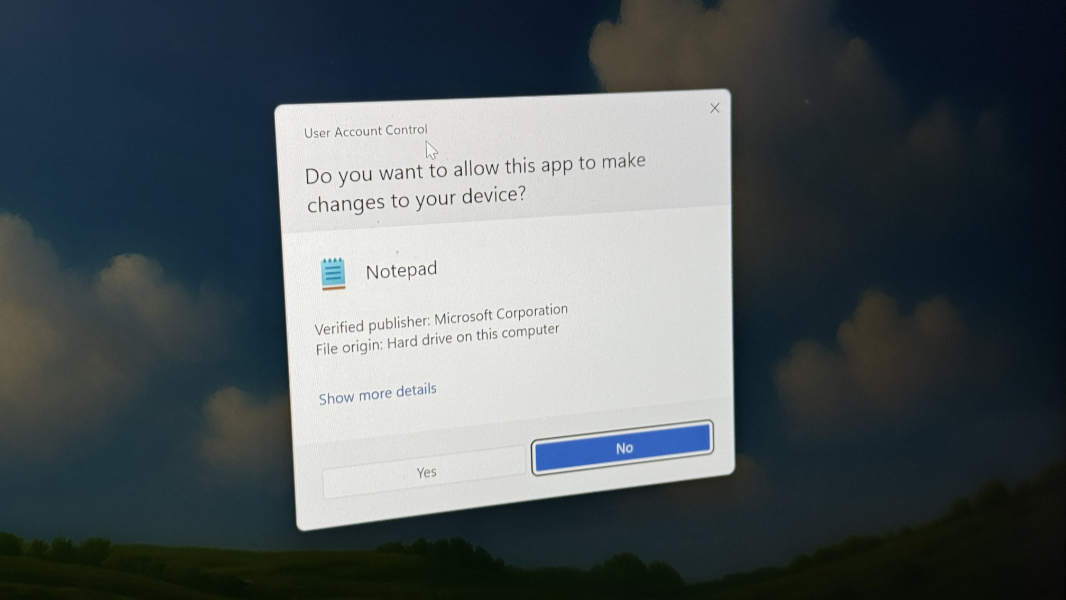
In the language of the day, UAC was all about “reducing the attack surface,” because reducing the privileges afforded to most apps and services helps protect against electronic attack. If your system is compromised by a worm, Trojan, virus, or other form of malware, that malicious code then runs with administrator privileges as well. That’s how PCs get “owned.” In more recent years, I’ve likened UAC to the middle, third brake light on automobiles: It’s an additional warning, in this case that you’re about to do something potentially dangerous. But it also happens frequently enough that many users have stopped worrying about it.
Microsoft architected UAC specifically to work within the context of the signed in user. That is, it understood that almost no one was going to create two accounts each time they set up a new PC, and then use the second (standard) user account for day-to-day work. So UAC works within the accepted way of doing things, where an individual uses a single (admin) account all the time.
UAC isn’t perfect. For compatibility reasons, it supports auto-elevation capabilities that bypass the prompt and can lead to bypass-based vulnerabilities. It was designed alongside the TPM chips that are now common in modern PCs but doesn’t require or use it. And it was designed before Windows Hello and, now, Windows Hello ESS, Secured Core PCs, and Copilot+, each of which adds major security protections to Windows. For these reasons and more, it was time for a more sophisticated approach to the admin account sign-in problem.
? What it does
Administrator Protection might be viewed as an evolution of UAC, but the way it works and the user experience are different enough to warrant the naming change. As with UAC, Administrator Protection assumes that a user will sign in to Windows using an admin account, and as with UAC, Windows 11 runs most apps and services using standard user account privileges when in this mode.
The internal differences are many and technical in nature, but the high-level overview is that Administrator Protection uses modern isolation techniques to better separate processes running with standard privileges from those running with admin privileges. The resulting security boundary prevents malware running with standard user privileges from compromising processes running with elevated privileges, a so-called bypass attack that was difficult but possible using UAC.
When the system or an app needs admin privileges, Windows 11 in Administrator Protection mode will prompt the user to authenticate using Windows Hello (by default). That’s a major change to the user experience, but it’s also a major change internally. Now, instead of elevating the process level for whatever app or task using the permission level of the signed-in user account, Windows fires up a one-time, non-persistent admin token when you prove that you’re you. The task runs in the elevated cocontext,nd then the admin token is destroyed so it can’t be used later by the same or different processes.
Administrator Protection also removes the auto-elevation capabilities in UAC. This means that its authentication prompts will be more frequent than has been the case with UAC: Users will have to authenticate every single time any process requires permission elevation. And while Microsoft recommends Windows Hello for its convenience and enhanced security, especially in Windows Hello ESS form, and enables this by default, it’s technically possible to disable it. That’s a horrible idea that would make this inconvenience even more inconvenient, as you would have to authenticate by password. So I will simply ignore that possibility here.
Administrator Protection seems like a no-brainer in some ways, and while UAC was met with derision almost 20 years ago, we’re at the point now where most would likely better understand why this type of protection is necessary. But as noted up top, Administrator Protection is disruptive. It’s even more disruptive than UAC was originally. And it will introduce problems for certain kinds of users that may make it less than desirable.
To understand why, we need to enable this feature first.
? Getting and enabling Administrator Protection
Microsoft announced Administrator Protection as a key advance in its Windows Resilience Initiative at Ignite 2024 last November. This past May, it provided more information about how Administrator Protection would wowork,nd it started rolling out the feature in preview through the Windows Insider Program. It’s disabled by default for now, and as of this writing, you can get Administrator Protection in the Beta (24H2), Dev (25H2), and Canary channels.
I’m curious to see whether it will be enabled by default in Windows 11 version 25H2 when that ships in a few months. For now, you can enable it by opening Windows Security and navigating to Account protection. If you see an Administrator protection section at the bottom of that page, that means you can enable it.
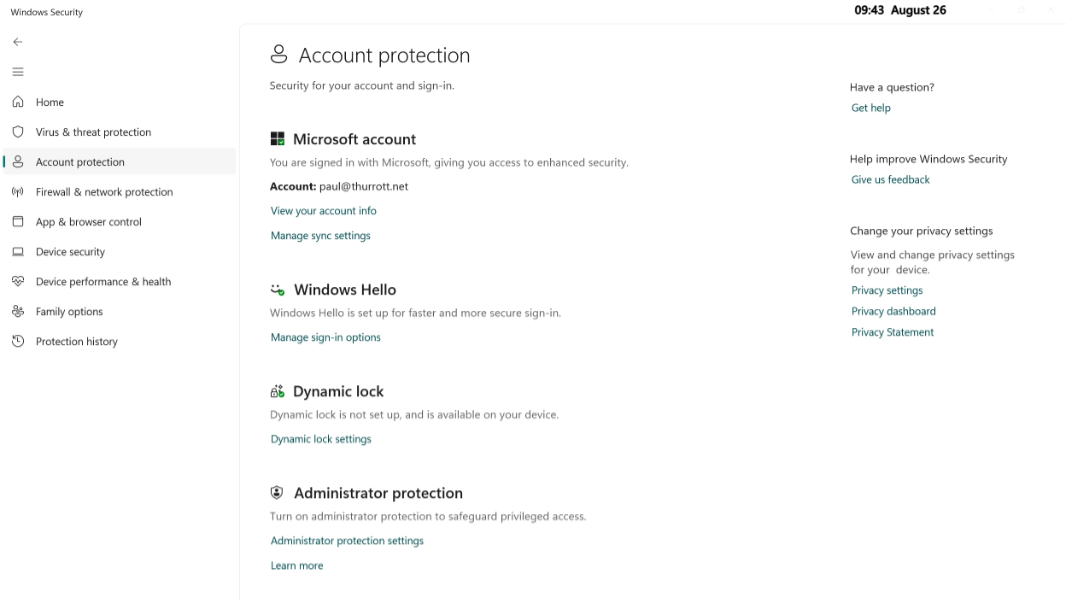
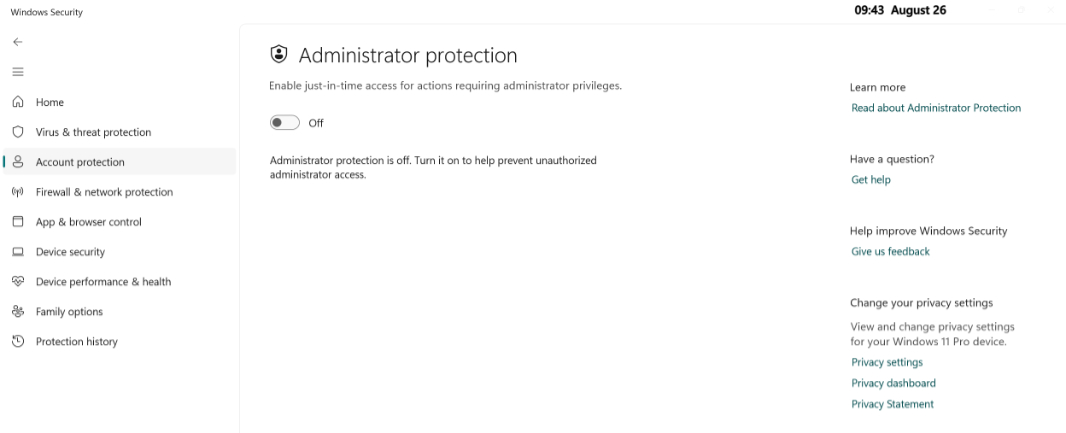
To do so, click “Administrator protection settings” and then toggle the only option on the resulting page, “Enable just-in-time access for actions requiring administrator privileges” to On.
This change requires you to restart the PC, so you should do that immediately.
? Using Administrator Protection
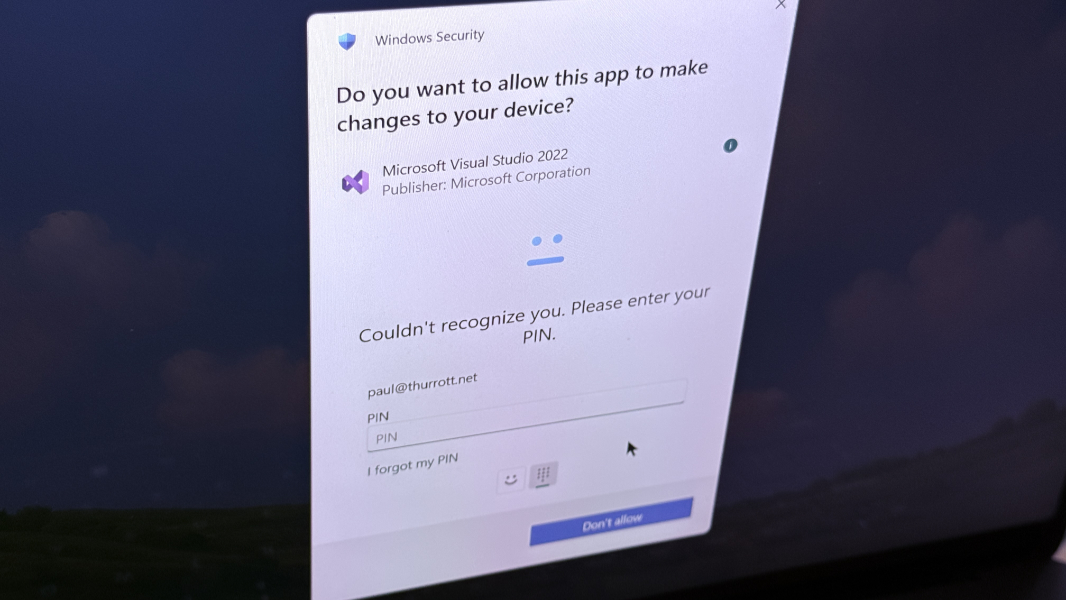
At first, you may not notice anything different with Administrator Protection enabled. But as you use the PC, you will notice the Windows Hello authentication prompts that appear, using the modernized Windows Hello user experience that Microsoft has been testing in the Windows Insider Program since late 2024.
This experience will differ according to which Windows Hello authentication exexperiences—facial recognition, fingerprint recognition, and/or PIN—your PC supports and which you’ve enabled. But it will quickly become familiar if you’re not used to it yet. In my experience, Administrator Protection authentication prompts are about twice as frequent as UAC prompts were previously. They are also a bit more disruptive because they require an extra step: Not only do you need to authenticate, but you also then have to click an “Allow” button in the prompt after authenticating.
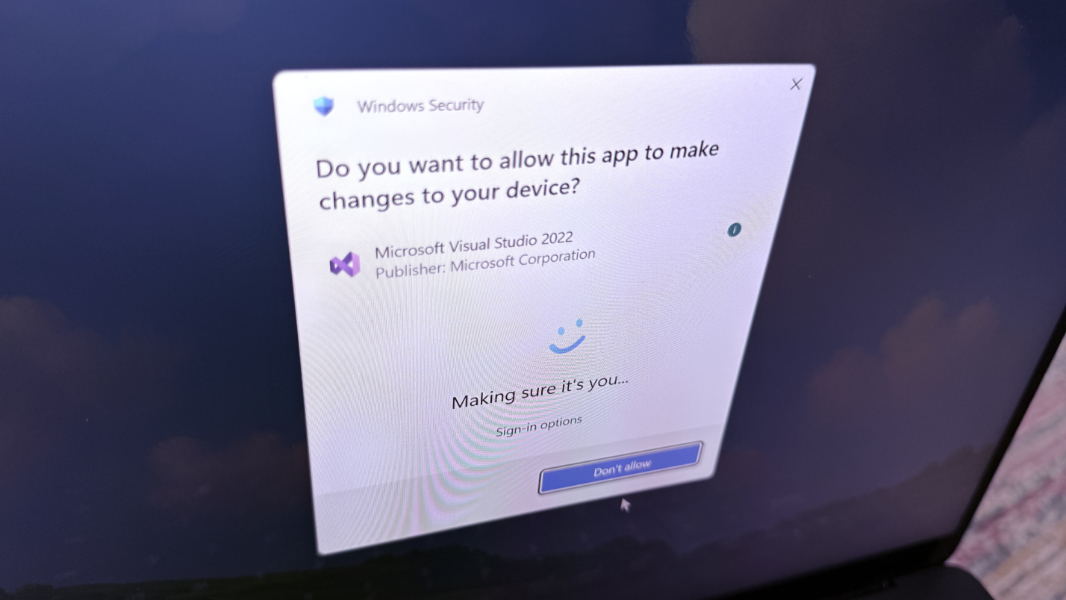
The easiest way to see this prompt is to try to run an app as an administrator. Previous to Administrator Protection, this action would trigger a UAC prompt. But now it triggers a modern Windows Hello authentication prompt. As such, it can failback to requiring a PIN if a biometric method doesn’t work or isn’t available.
Depending on how you use the computer, this may or may not be problematic, at least beyond the annoyance of this Windows Hello authentication experience.
? When Administrator Protection gets weird
When you authenticate with Windows Hello to allow some app or process to temporarily run with admin privileges, that app or process is no longer running under your user context. If you’re, say, changing the time in the Settings app, this isn’t a big deal. But if you’re doing anything with an app that works with the file system, some curious problems emerge.
As a simple example, when you run Notepad normally and type Ctrl + S to save a file, the Save as dialog that opens will display the contents of your user account’s Documents folder by default. From there, you can save the file or optionally navigate to a new file system location first.
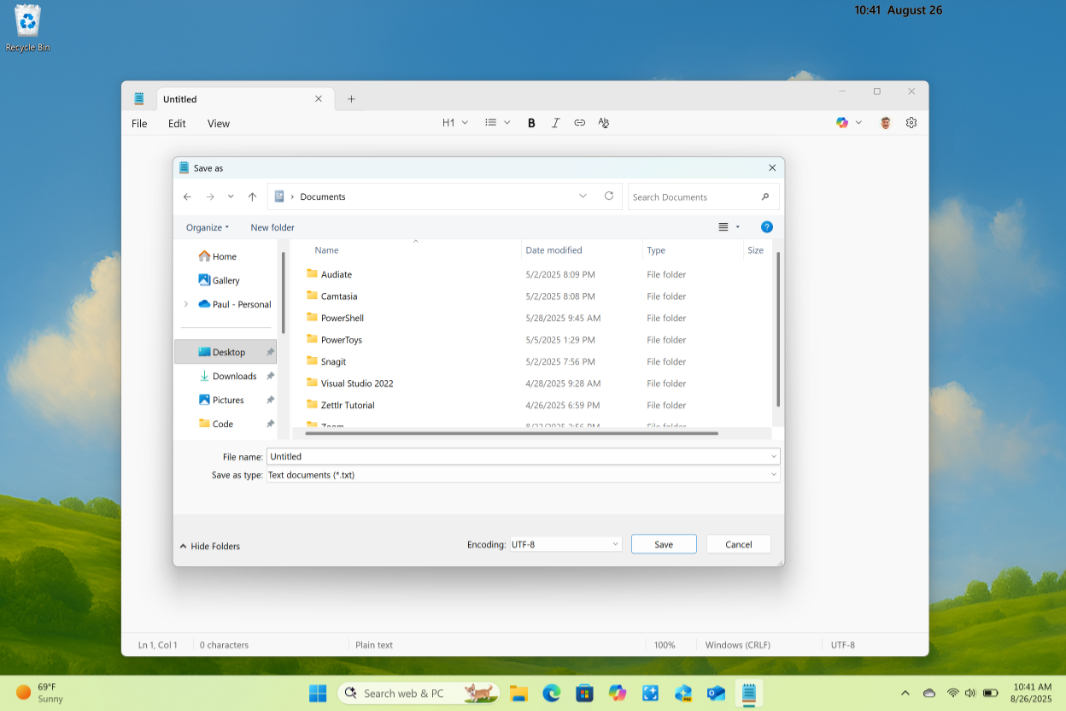
When you run Notepad using admin privileges, authenticate with Windows Hello, and then type Ctrl + S to save a file, the Save as dialog that appears can’t access your Documents folder or whatever previous location you used. And so it displays the root of the file system instead.
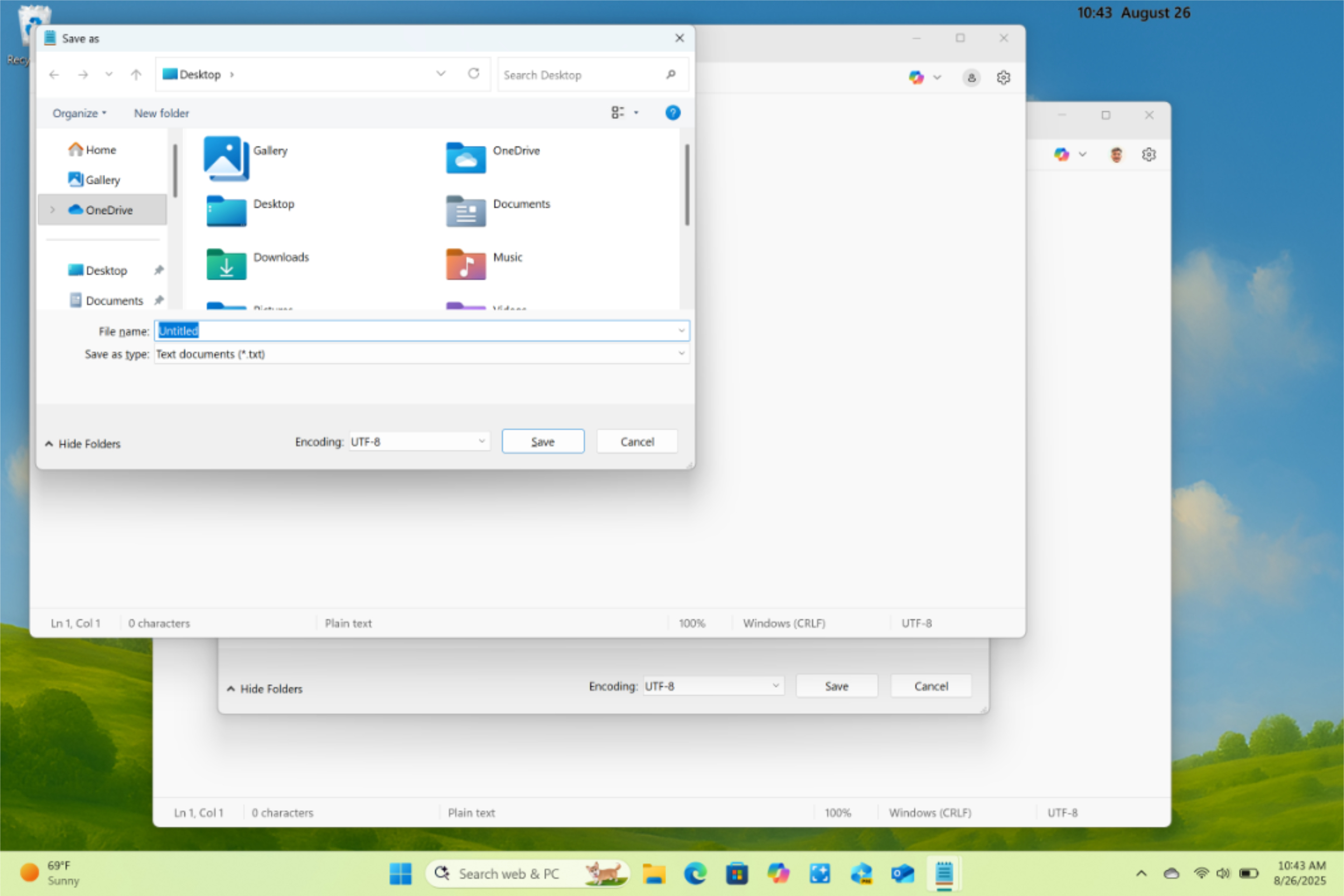
But this isn’t the root of the file system for the signed-in user account. It’s the root of the file system as seen by the temporary access token. So you can still get to your Documents folder (it does have admin rights), but you will need to go through the file system to get there. That is, you can’t click the Documents folder in the navigation pane. You have to navigate manually to C:\Users\Paul\Documents (or wherever).
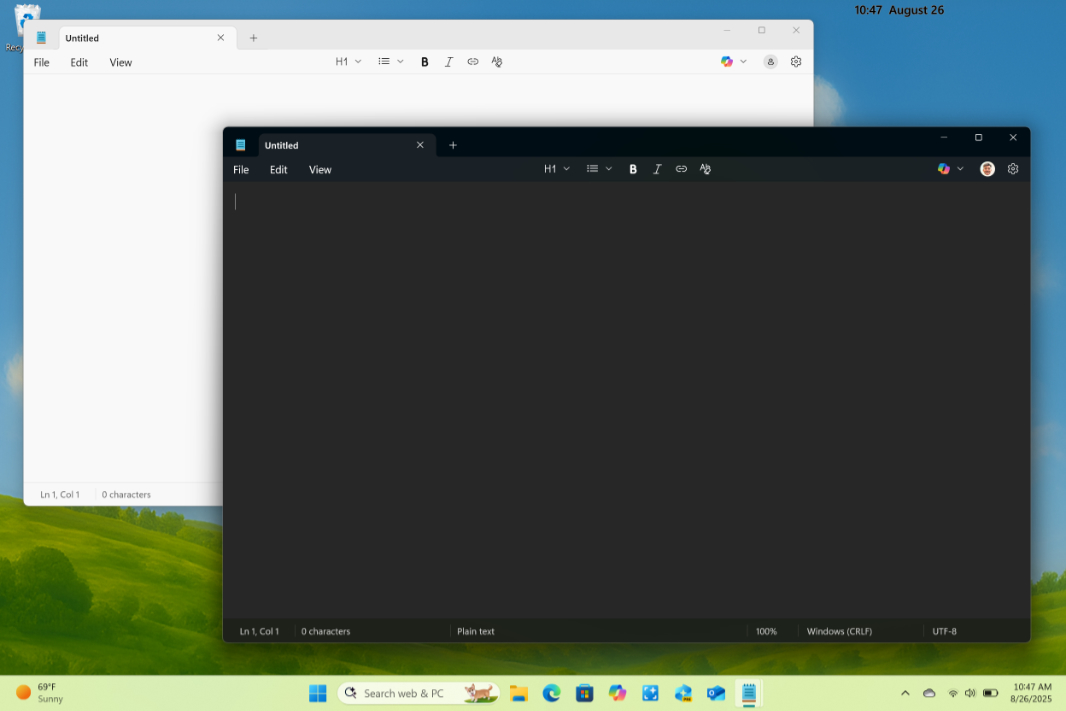
You can see this with the Registry as well. If you change Notepad to use the Dark theme, the Notepad app that’s temporarily running with admin privileges remains on the Light theme. That’s because they’re not associated with the same user, and Notepad settings are stored per-user in the Registry.
You don’t see that everyday. But maybe now you will.
⛓️? When Administrator Protection falls apart
That’s weird, but most users will likely not notice or care. (That said, I could imagine someone saving a file in some part of the file system as a temporary admin and then not being able to find it later.) But I’ve noticed more serious issues when trying to use Visual Studio, Microsoft’s developer IDE, with Administrator Protection. The apps I create with Visual Studio don’t work anymore.
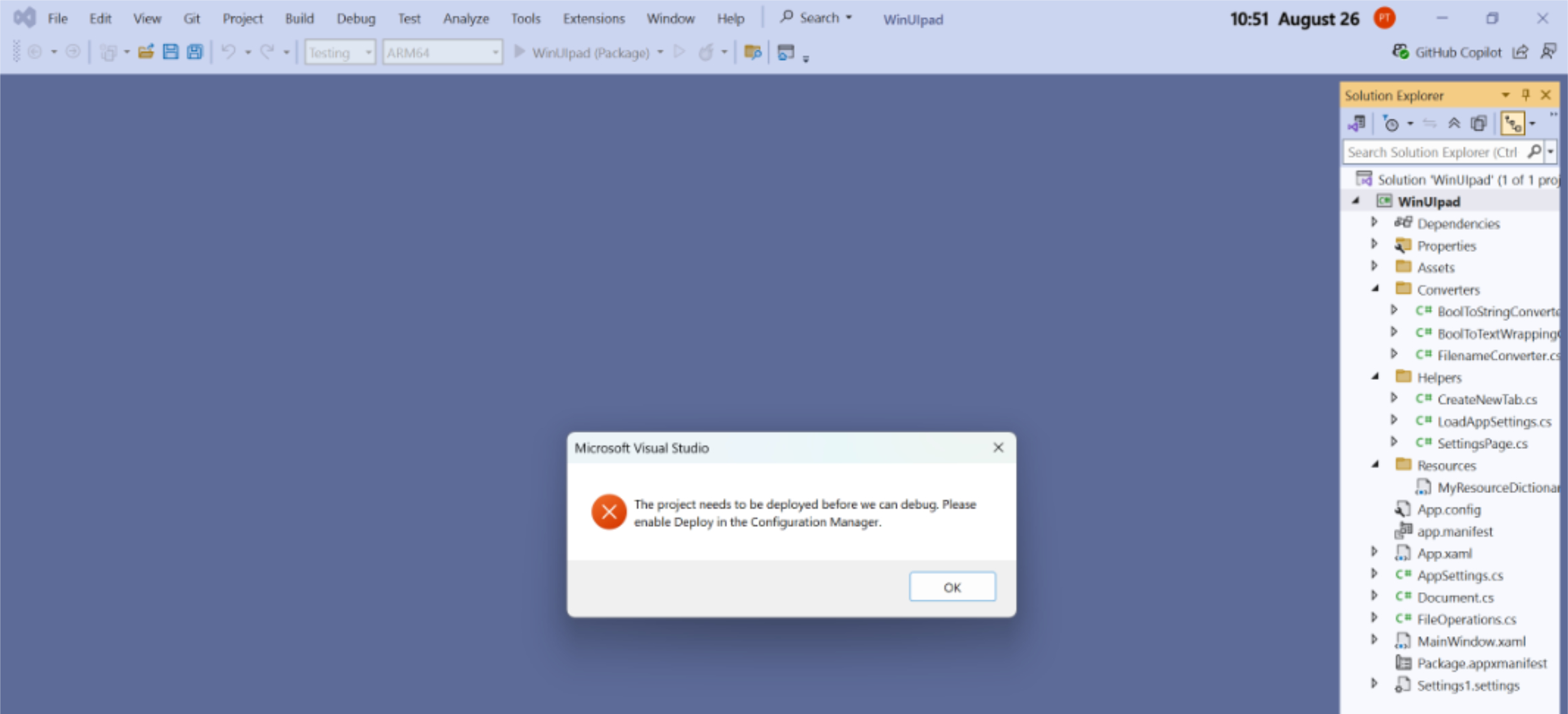
The issue here, I think, is a familiar one: Visual Studio—or Microsoft Office, or whatever complex app–can run with standard user privileges, but various extensions may not. Oddly, running Visual Studio as an admin doesn’t solve this issue, but Microsoft says that’s by design and that it does not support this configuration. Basically, your mileage may vary.
This is particularly problematic because app compatibility issues will need to be fixed, and the only way to do that, as a developer, is to use Visual Studio. Microsoft recommends that developers revisit their Windows apps to ensure that features that require elevation authenticate on demand, not each time the app runs, and don’t require silent, pass-through elevations, as those will fail.
? Two steps forward, one step back
Administrator Protection appears to solve a long-standing security problem in Windows, but it will be disruptive in the short term. The level of disruption will depend in part on what you do with your PC—i.e., which apps you use—but will be a bit more annoying than UAC, even when everything works fine: That modern Windows Hello authentication experience takes longer to get past, and it requires extra steps. And that’s a problem because most people are lazy and prefer convenience over security.
The success of this system will depend largely on whether Microsoft enables it by default when Windows 11 version 25H2 arrives. As with Smart App Control and Ransomware protection, two other Windows 11 security features that are also accessible via the Windows Security app, my guess is that it won’t do so. In time, all three of these features will hopefully be enabled by default, but this will likely wait on some convenience/compatibility threshold being reached.
Until then, it’s up to us individually to assess Administrator Protection for ourselves and see how or whether it impacts our daily workflows. My advice is to at least try. And if you’re using a workplace or school PC, you may not even have a choice, of course, since this feature may be enabled for you by the IT staff.
The good news is that you can toggle it on/off as needed as an individual. So if Administrator Protection prisroblematic, you can just turn it off and reboot, and everything will go back to the way it was. And unlike with Smart App Control, you can do this repeatedly, as required. That, at least, is a good design decision.
Gain unlimited access to Premium articles.
With technology shaping our everyday lives, how could we not dig deeper?
Thurrott Premium delivers an honest and thorough perspective about the technologies we use and rely on everyday. Discover deeper content as a Premium member.