Passwordless Password Manager Problems (Premium)
- Paul Thurrott
- Jan 11, 2024
-
15
The problem with security products and technologies is that they’re often too difficult to use, causing people to give up on them. This is why I’m so excited about passkeys, a new passwordless authentication technology for online accounts that is both secure and convenient, and is thus already being adopted by online services and their users at a rate not achieved by more complex security solutions like security keys and authenticator apps. And it’s why I’m so unhappy with password managers, which in my experience are too difficult to use, especially in their default configurations.
This is going to change. All the leading standalone password managers have announced that they will allow their users to securely unlock their vaults using locally stored passkeys instead of forcing them to remember and type a master password. In doing so, password managers will become passwordless, and this configuration is in many ways the holy grail of security in that it is—or will be—both secure and convenient.
In the meantime, we have to deal with the password managers we have today. And while the two top-rated password managers—Bitwarden and 1Password—do provide passwordless experiences on smartphones thanks to their integration with the integrated biometric- and PIN-based sign-in methods on those devices, the experience in Windows is less ideal. Bitwarden lets you unlock its password manager using Windows Hello PIN or facial or fingerprint recognition, but the experience is so complicated and unreliable that I literally spent weeks trying to make it work consistently across multiple PCs. And 1Passkey released a public beta version of its password manager in mid-December that only supports passkeys (meaning there’s no password or secret key), introducing its own complexities. Key among that it’s incredibly unreliable, doesn’t work like other passkeys, and requires you to create a new account. (That latter issue will be resolved by the time this feature exits beta.)
Neither product is both secure and convenient, no standalone password manager is (in Windows). But when Bitwarden works, it is what I think of as convenient enough. The good news is that once it works, it works well, and this configuration doesn’t require any security compromises. Which I will get to below.
What led me down this path
First, though, I’d like to discuss how I got here.
This has been a long and frustrating journey because security is difficult. Difficult to configure correctly. Difficult to replicate that configuration across multiple devices. Difficult to explain to others. And it’s in a state of flux. The industry has taken multiple steps over the years to achieve a passwordless future in which easily guessed and frequently reused passwords are no longer necessary. And with passkeys, we’re finally get there thanks to its perfect blend of security and convenience.
This is great. But security is like any other kind of technology in that the introduction of something new and better doesn’t mean that the old ways of doing things suddenly disappear. Instead, we’re in a transition period during which we will have accounts with any number of configured sign-in methods, including passwords, authenticator apps, passkeys, and more. And it’s on us, sadly, to navigate this mess.
So I’m trying to figure this out.
But it’s hard. Back in December, I was writing what became two new chapters in the Windows 11 Field Guide—Secure Your Microsoft Account and Passkeys and Security Keys—and I encountered a problem I rarely experience, a sort of writer’s block triggered by worries that I wasn’t a subject-matter expert and was thus unqualified to advise others. The only thing worse than misconfiguring my own online accounts, I thought, would be causing others to do the same through a mistake or poorly-written article.
It started out normally enough, with me doing what I always do. Test and retest, on multiple PCs, in different configurations, and with different accounts and account types. As always, I was looking for consistency, the same results everywhere when following the same set of actions. In 30 years of writing about personal technology, this has always been the goal, but it’s all the more important when it comes to anything related to security, especially online account security.)
My obsession to get this right was perhaps only exceeded by my obsession to explain it properly, in plain English, in a way that I hoped even mainstream, non-technical readers would understand. This led to another unusual experience for me in which I re-wrote the same passages multiple times, again and again, in an effort to arrive at the not just the right words but the right order in which to explain things. In doing this, the single chapter I had originally intended to write expanded into two chapters and also triggered my writing, so far, three articles for this site, Tip: Properly Secure Your Microsoft Account, The Secret Lives of Passkeys (Premium), and Tip: Use Passkeys With Your Microsoft Account.
There will be more: As I wrote and re-wrote, I kept bumping into related topics that also warrant attention. Key among those is password managers, and as I looked at my own use of password managers, I saw something I hadn’t seen when I reviewed the security of my several Microsoft accounts (and those of my wife) or that of my PCs and devices, each of which is configured with secure PIN- and biometric-based sign in methods. I saw configuration mistakes and inconsistencies that I didn’t like one bit. And so figuring out my password manager became a new obsession, something I needed to get right for me.
There’s little reason to explain everything I went through trying to get Bitwarden to work consistently across all of my PCs and devices and in a manner that is equal parts secure, convenient, and consistent across devices, a holy trinity of sorts when it comes to anything security related. All that matters is that I failed to do so at the time, and that I now know that it’s not me: This thing really doesn’t work reliably or consistently when it comes to configuring it for passwordless authentication in Windows.
Two weeks ago, I didn’t know that. And so I experimented with the stable version of 1Password, which has a simpler and cleaner UI than Bitwarden but doesn’t offer secure passwordless sign-ins, and then the 1Password beta, which supports passkeys. And that sounded ideal to me until I tried it. The first hurdle was that you can’t add passkey support to an existing 1Password account, and instead have to create a new account. (As noted, this will change when passkey support exits beta later this year, 1Password says.) That I can deal with—moving the contents of one 1Password vault to another is easy—but this system is so balky and unworkable that I struggled for several hours, deleting and recreating this new account at least three times, before I was able to authenticate on a second device using the passkey from the first. Based on this experience, I can’t recommend the beta to anyone right now because it’s a disaster that subverts a key benefit of passkeys, their seamless integration with the secure sign-in methods provided by your smartphone and PC.
And so I asked people we all know, people I trust—Brad Sams, who uses 1Password, and Richard Campbell and Leo Laporte, both of whom use Bitwarden—how they configure their password managers in Windows (or on the Mac, in Leo’s case). And their answers were enlightening. Each uses a master password to sign in to the password manager, and that’s usually required after a reboot, but can also occur after a timeout period. And Richard and Leo both use incredibly long—like, 30 characters in length—master passwords, which astonishes me. I can barely type a 4-digit PIN without making a mistake.
Put simply, their password manager sign in methods are secure but inconvenient, and that means that most people out in the world, and most people reading this, will never do such a thing. Most people who try a standalone password manager and have this experience will probably stop using it. And the chances of anyone trying that type of product again later is low.
And that sucks. Because …
Everyone should use a password manager
This simple assertion, as obvious as it seems, is nonetheless muddled by a long list of nuances that serve to confuse matters. For example, most of us are likely using multiple password managers because there’s one built into each web browser and each personal computing platform in addition to third-party, standalone solutions. And this proliferation of password managers gets even more complicated for people like me who use or have used multiple web browsers across multiple platforms. So when I say that “everyone should use a password manager,” what I’m really saying, or am also saying, is that everyone should use one password manager.
And only one.
I know what you’re thinking: You are literally only using one password manager. The issue is that when you switched to whatever password manager you’re using now, you almost certainly didn’t remove the passwords from all the password managers you used in the past. I bet you can’t even remember them all, and some of them are likely tied to dead products and platforms like Windows Phone or Internet Explorer. And this issue, which you may have never even considered, leads to all kinds of uncomfortable thoughts. Like this little gem: Because you can’t be sure that you emptied every password manager you’ve ever used, you might have to take on the tedious and time-consuming task of literally changing the password/sign-in methods you use for every single online account you use while also deleting the other accounts, at the source, that you no longer use. (I know, gross. More on this in a bit.)
You should really use a password manager.
As noted, password managers do much more than that humble moniker suggests. Yes, password managers manage passwords, meaning they provide a secure, automated, place for storing the usernames and passwords associated with each of your online accounts. But they also evaluate the passwords you use, identify those that are weak or reused, or have been compromised, and then help you fix that. They can generate secure, complex passwords for new or existing accounts. They can be used to autofill those usernames and passwords when needed in websites and apps, on desktop and on mobile. And they can store and autofill other important data, like credit card numbers, addresses, and more, and can autofill that data when needed as well. So look past the basics and make sure you’re using your password manager fully, so you can securely automate as much as possible.
You should use the right password manager.
Though I have experience with the passwords managers in every web browser I’ve ever used, I haven’t evaluated every password manager out there. But this one is simple enough: The “right” password manager is the one that meets your needs, meaning not just that it provides all the expected features, but that it does so everywhere you need it. And it should do so now and in the future: Because our needs changes over time, as do the computers and devices we use, that password manager should be portable and not locked into a single ecosystem. It should work everywhere. This is best achieved with standalone password managers, though one could make an argument for the few cross-platform web browsers like Google Chrome that also provide autofill capabilities on rival desktop and mobile platforms too. (Also, exporting and importing to move between password managers isn’t horrible in my experience.)
You should use a password manager correctly.
In this context, correctly means securely, with the caveat that no one will do anything truly secure unless it’s also convenient, meaning that it’s as seamless as possible. It’s the reason I know—and all of us know—otherwise intelligent adults who literally disable the PIN lock on their phones, computers, Kindles, and other devices: Security is seen as being a nuance, something that gets in the way, rather than being something necessary that keeps you safe. But digital security should be viewed like a seatbelt, motorcycle helmet, or any other physical security method: When used correctly, it can be both secure and convenient enough. And even security measures that slow you down a bit become second nature in time.
Standalone password managers are not convenient. And this is a problem.
Yes, it’s always been a problem. But in a bit of interesting timing, LastPass announced recently that it now requires all customers to use a master password with at least 12 characters, setting off a visceral reaction from me that was tied to my recent experiences with securing my Microsoft accounts and figuring out how passkeys really work in Windows 11.
“The Achilles Heel of all password managers is that they still rely on users having a master password to protect their personal data,” I wrote. “Here we are in 2023, configuring as many accounts as possible to be passwordless with technologies like two-step verification and passkeys, and yet somehow the vaults that store our account passwords, credit card numbers, and other important data still use … a password? This makes no sense to me: Password managers should support and require the same two-step verification techniques that we use to protect our other online accounts, and they should give us the option to go completely passwordless by not even using a master password in the first place. Which is easily hacked no matter the length.”
And there it is.
What I expect from a password manager
As noted, standalone password managers are not configured to be seamless or convenient in Windows by default, despite the fact that our PCs have TPM security chips and can be configured with secure Windows Hello sign in methods that create the end-to-end secure environment needed for passkeys. (This works much better on mobile, go figure.) For this reason, people will never use them, or they will disable security to some degree to make the experience more seamless. For example, you could configure Bitwarden or 1Password to never lock their vaults and rely on your common sense and the PC’s security features to keep their contents safe. But please don’t do that. You can achieve a configuration that is convenient enough today with either product and be secure too. You just need to work at it.
Here’s what I am trying to do:
- Use one password manager across all my PCs and my phone
- Automatically or seamlessly unlock that password manager’s vault when I sign in to a device
- Configure that password manager to be the only autofill provider on all of my devices
Once this system is up and running, I will move on to:
- Figure out the best method to remove the passwords from other browsers/password managers
- Evaluate the stored accounts in the password manager and change passwords and/remove out-of-date accounts as needed
This will require a bit of work.
I finally figured out Bitwarden
It’s not possible to configure Bitwarden to automatically unlock when I sign in to my PCs. Instead, you can disable security entirely by never locking the vault—which I won’t do even though I trust myself and the secure sign in methods provided by Windows—or you can unlock the password manager vault using Windows Hello when you reboot or sign in to Windows. I chose the second option, which falls into that “convenient enough” category I invented, but I would like this to work more seamlessly in the future.
To unlock Bitwarden (or 1Password or any other password managers, for that matter) with Windows Hello, it’s not enough to use its browser extension, you also need to install its desktop app. This is because browser extensions are not full-featured apps and cannot directly integrate with system features like Windows Hello. And this fact raises some interesting issues. This wouldn’t be necessary if these products just supported passkeys natively. You don’t need to do this on mobile because password managers are apps on mobile, so they can access any and all system features. And this extra step is yet another example of why the inconvenience of standalone password managers makes them off-putting to people. They require work.
To unlock Bitwarden with Windows Hello, you have to configure it correctly, both in the extension and in the app. And this is where the user experience falls apart. As Richard noted when we discussed this yesterday, Bitwarden is a perhaps a classic example of a solution made by people who are security experts, not user experience experts. And based on my experience, you will fail at getting this right, perhaps many times, before you succeed. But the results, I think, are worth it.
The basic steps are:
- Install the Bitwarden web browser extension and desktop app, and sign in to each with your username and master password. (I have configured Bitwarden to use two-step verification through an authenticator app as well, so each time I sign in to the service, I have to type a code I get from that app. Once Windows Hello authentication works, that will no longer be required.)
- In the app, configure Bitwarden to “Unlock with Windows Hello” and “Ask for Windows Hello on app start.” Windows Security will prompt you to authenticate with Windows Hello.
- In the app, enable the following app settings: Start automatically on login and Allow browser integration.
- In the app, optionally enable the following app settings: Show tray icon, Minimize to tray icon, Close to tray icon, and Start to tray icon.
- In the extension, enable “Unlock with biometrics.” You will need to click “Allow” in a permissions dialog and then authenticate with Windows Hello. (If you prefer using a PIN
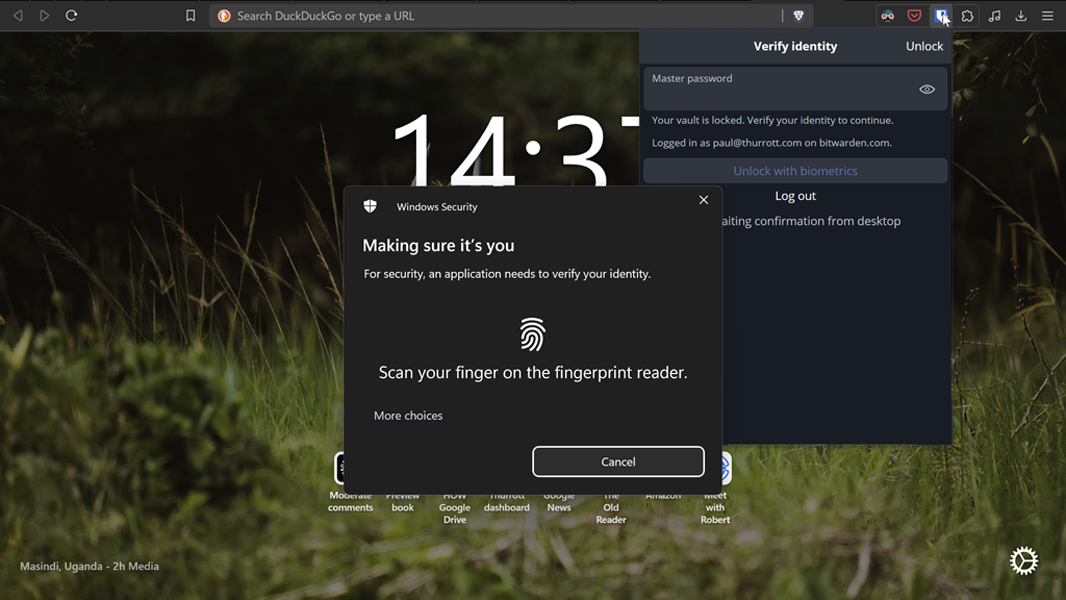
Sounds easy, right? The issue is that all kinds of things can go wrong throughout that process. One of the most common issues I’ve seen repeatedly is that I followed the steps above only to be told that “browser integration is not set up” and that I have to configure that in the app. Which I had already done.
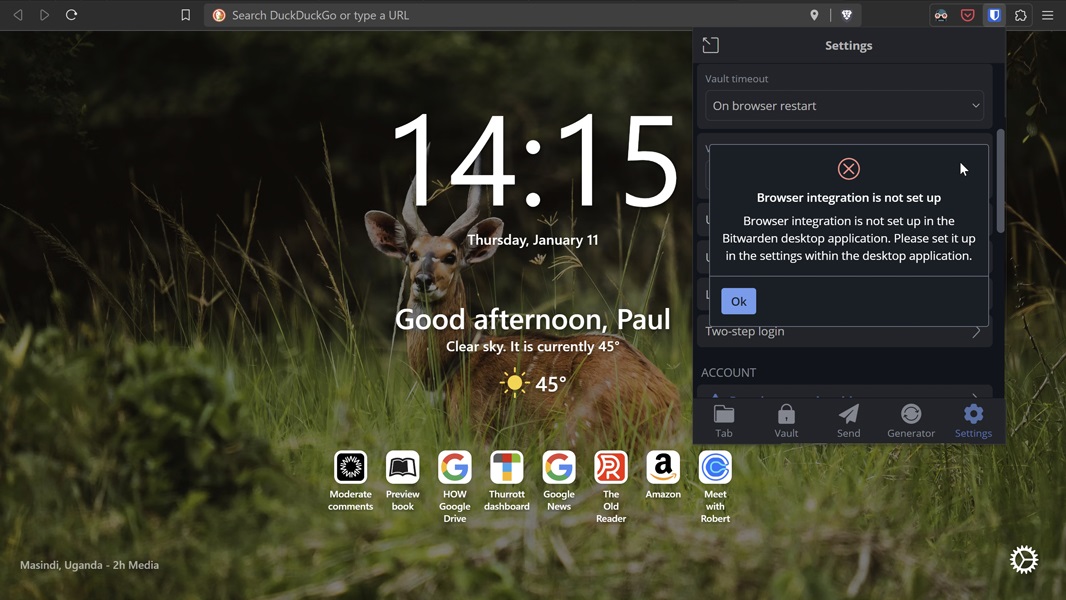
The trick here is to just keep trying: Disable and then re-enable “Allow browser integration” in the app’s settings repeatedly until you make it work. You’ll know you got it right when the Windows Security window appears, asking you to authenticate with Windows Hello.
Once it’s configured, you need to test it. To do so, close all of your open applications, sign out of Windows or reboot, and then sign in again. When you open your web browser, you will see that Bitwarden is locked. But when you click its extension icon and the sign-in panel appears, a Windows Security window will also open, letting you authenticate with Windows Hello. You’re in. Not seamlessly, but conveniently enough.
I will try 1Password again when passkeys work, with the goal of turning convenient enough into seamless. We’ll see. But meanwhile, I have those other tasks to tackle. My online accounts and their passwords are still in too many places, and many will need to culled or updated. That’s a task for another day.
Gain unlimited access to Premium articles.
With technology shaping our everyday lives, how could we not dig deeper?
Thurrott Premium delivers an honest and thorough perspective about the technologies we use and rely on everyday. Discover deeper content as a Premium member.