2026 Security Checkup: Authenticator App ⭐
- Paul Thurrott
- Jan 19, 2026
-
0
Each of your online accounts supports different ways for you to sign-in and verify your identity. As a general goal for each account, especially the important accounts tied to identity that store payment methods and other personal information, you should configure multiple methods to sign-in and verify when possible and try to use the most secure and convenient of those methods when possible.
The most secure ways to sign-in and verify your identity are all forms of multifactor authentication (MFA), sometimes called two-factor authentication (2FA) or two-step authentication. The most convenient forms of MFA are those that provide passwordless capabilities. And of those, the two best methods are passkeys and authenticator apps.
An authenticator app is an app you install on your phone and/or other mobile devices (and, in some cases, computers) that provides an additional layer of verification, or factor, to your online accounts. As with other MFA solutions, this prevents hackers or other malicious actors from getting into an account that has been compromised, even if they have your username and password.
You manage the passwords (really, usernames and password combinations) and passkeys for your online accounts with a password manager. In a similar fashion, you use an authenticator app to manage second-factor verifications for your online accounts. The two work together, with the password manager providing the initial sign-in credentials and the authenticator app handling the additional verification that proves you are you, letting you into the account.
✅ Tip: I will be writing about password managers soon, but you can reference Password Management Basics (Premium), an earlier post, if you need more information now.
Authenticator apps work by creating a connection, or secret key, between an online account in the cloud and the app on your device. Most authenticator apps create dynamic time-based one-time passwords (OTPs) (or codes) that refresh every 30 seconds. When you attempt to sign-in to an online account on your computer, you will be prompted to enter a code from that app. So you will authenticate yourself on the phone (and/or the app itself), locate the code for that account, and then type it in on the computer.
✅ Tip: I wrote “most” above because Microsoft accounts (MSA) support a different form of 2FA that’s even more convenient, but you have to use a Microsoft app for that. This is described later in the article.
Keep your password manager and authenticator app separate
Though some password managers offer authenticator app capabilities too, you should use separate password manager and authenticator app solutions. This is not about a single point of failure. It’s because the core security principle behind MFA is having separate “something you know” (e.g. a password) and “something you have” (e.g. a device) factors. When you sign in to an account on your PC, the password manager is on the PC (an app or a browser extension) and the authenticator app is on your phone.
But it’s not just that. For the best possible security, you should secure your password manager with an authenticator app too. And you cannot do that by using the password manager as an authenticator app. That would be like storing the key for a safe in that safe. It’s impossible.
Which authenticator app?
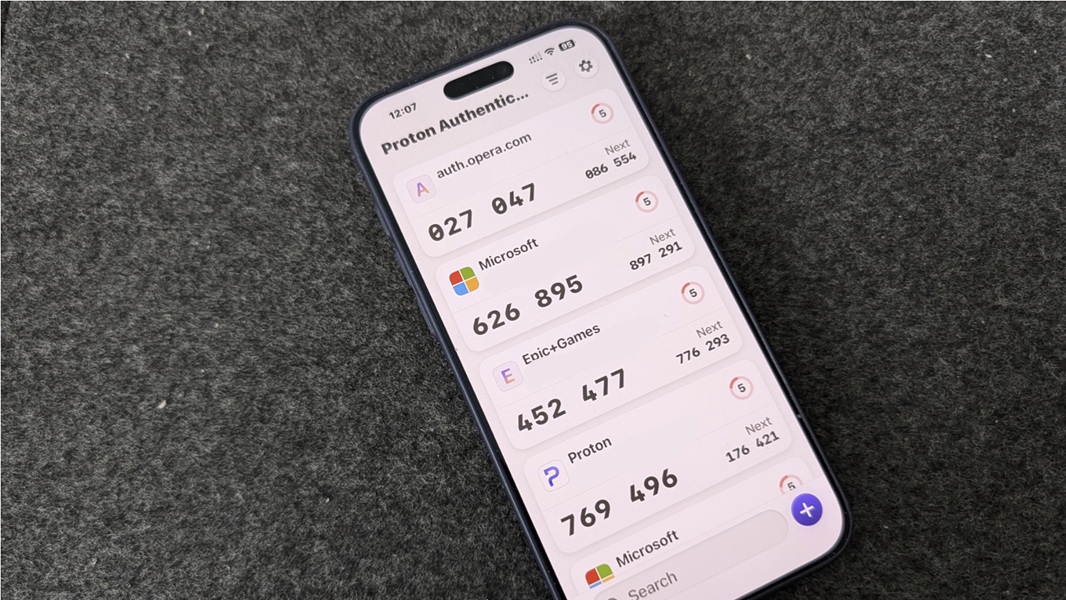
You want an authenticator app that is both trustworthy and portable, and there is only one such authenticator app that I’m aware of: Proton Authenticator. This app is free and open source, fully encrypts the syncing of your account codes (for safety and portability), doesn’t track your activity, and is available everywhere, including Android, iPhone, iPad, Windows, Mac, and even Linux. It’s what I use, and it’s what I recommend.
I can’t imagine why you wouldn’t use Proton Authenticator, honestly. But The Wirecutter recommended two other solutions, Duo Mobile and Google Authenticator, before Proton released its Authenticator app. I have used Google Authenticator and it works well, though it doesn’t fully encrypt account code sync, if that’s an issue for you.
You might want two authenticator apps
We all have at least one foot in the Microsoft ecosystem here. And anyone with a Microsoft account (MSA) will want to use the Microsoft Authenticator app, if only for that one account, for the reasons described below. So even if you choose Proton Authenticator for all your other accounts, I recommend using Microsoft Authenticator in addition to that.
You could of course use only the Microsoft Authenticator app. But it’s not as portable or trustworthy as Proton Authenticator.
How to use an authenticator app
After installing Proton Authenticator or another (non-Microsoft Authenticator) authenticator app on your phone, you can begin adding accounts to it. How you do so will vary by online account, but from a high level, you will sign in to whatever online account, access the security section in account settings, and find an MFA, 2FA, authenticator app, or similar option. Most identity-related accounts, like those provided by Amazon, Google, and Microsoft (but not, notably, Apple) support authenticator apps. As do services like Facebook, X/Twitter, and many, many others.
As an example, you can add an authenticator app to your Amazon account by signing in to Amazon.com in your web browser and navigating to Accounts & Lists > Accounts to view the Your Accounts page. Then, click Login & security and sign-in as required and navigate to 2-step verification to view Two-Step Verification (2SV) Settings.
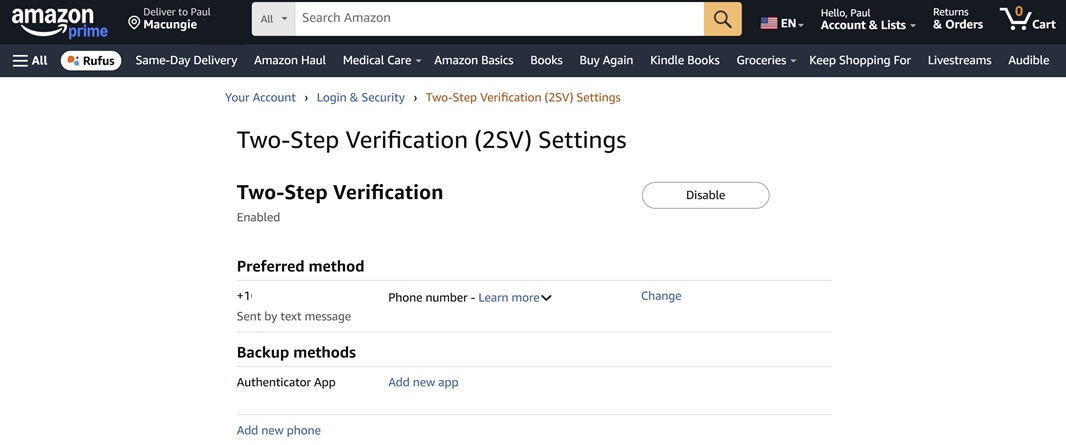
If two-step verification is not enabled, do so. Then, you can add your Amazon account to your authenticator app by clicking the “Add new app” link next to “Authenticator App” under “Backup methods.”
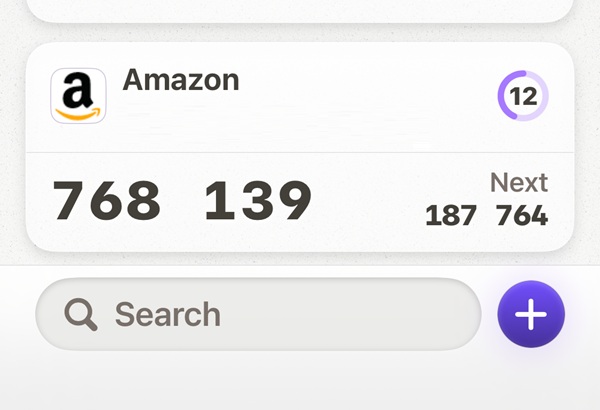
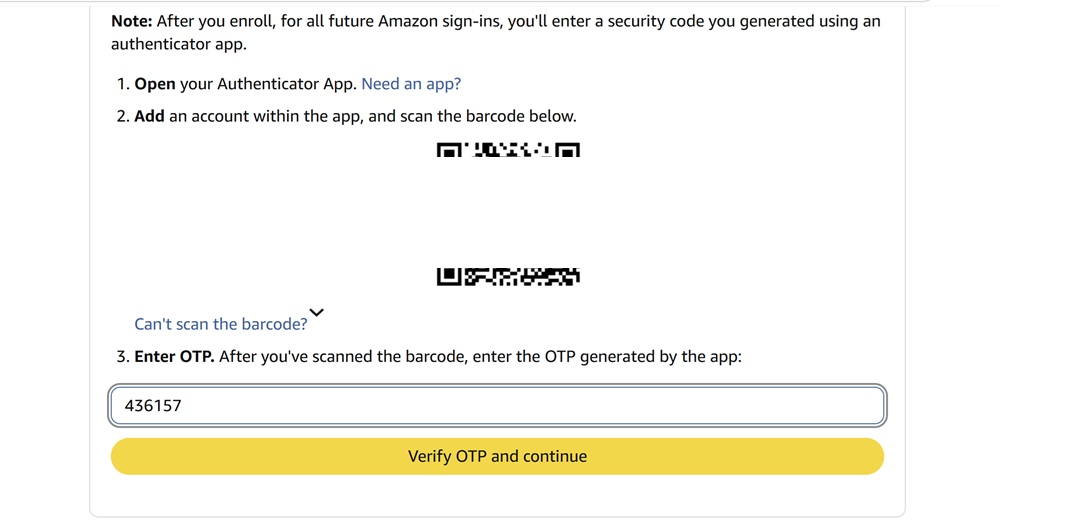
Amazon will display a QR code. Pick up your phone and authenticate, then launch its Camera app to scan the code. This will open your authenticator app and add the Amazon account. In Proton Authenticator, you can see the new account at the bottom of whatever accounts you’ve configured in the app. This account will have a name, a username, a time-based temporary code, and a countdown timer indicating how long that code is still valid.
On the Amazon website on your PC, enter the code displayed for that account in the authenticator app. Then, click “Verify OTP and continue” to complete this process.
To use the code, sign out of Amazon in the web browser on your PC (or, for testing purposes, just open an Incognito browser window or similar). Then, sign-in normally: Amazon will prompt you to enter your username (email address) or phone number and then your password (or your password manager will handle this automatically).
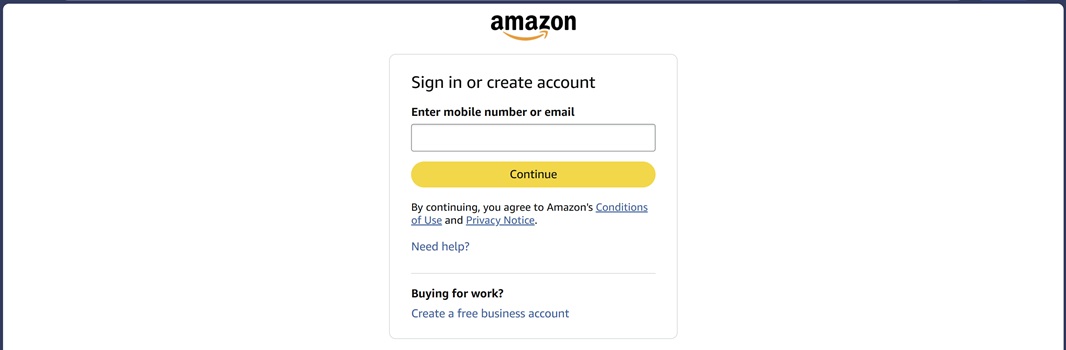
Now, Amazon will prompt you to enter a two-step verification code. If you previously configured a phone number with your account, it will default to that. But you can cancel that and choose a different method. (And this will be the last time you need to do that.)
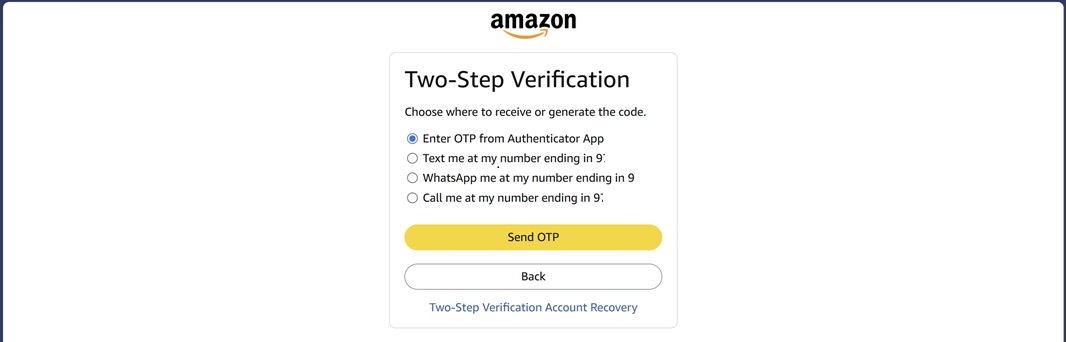
Select “Enter OTP from Authenticator App” and click “Send OTP.” Then, enter the code displayed in your authenticator app as prompted and tap Enter to sign-in.
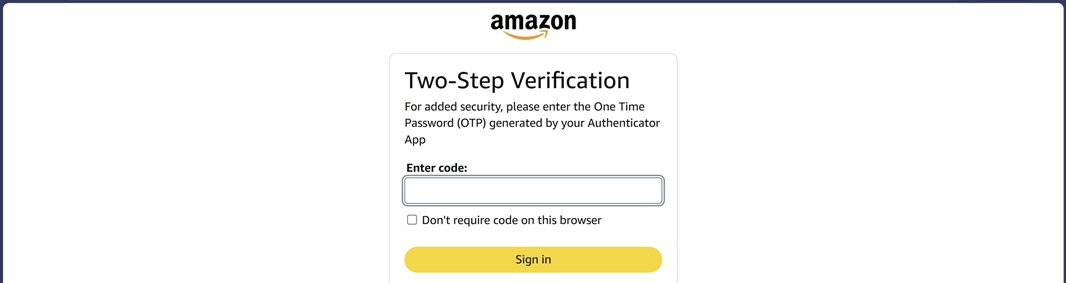
That’s it. You’re in. Future authentications will be faster and simpler. And other accounts offer a more seamless sign-in experience. But even Amazon isn’t that bad: If you use a password manager, the username and password will autofill and then all you have to do is enter the code from your authenticator app.
Finding out which accounts work with authenticator apps can be a bit difficult. But some password managers, like 1Password, will identify those accounts that are compatible with authenticator apps. I currently use dozens of accounts with Proton Authenticator, including Activision, Epic Games, Facebook, GitHub, Mint Mobile, Mozilla, Opera, PayPal, Proton, Slack, Stripe, Synology, Twitter/X, and many others.
How to use Microsoft Authenticator
You can use Proton Authenticator or another authenticator app with your Microsoft account (and I describe that briefly in 2026 Security Checkup: Microsoft Account ⭐). But the Microsoft Authenticator app is much more seamless, and it offers a truly passwordless sign-in experience.
To add your Microsoft account to Microsoft Authenticator, you can follow the instructions in 2026 Security Checkup: Microsoft Account ⭐. Or, you can do so directly from the app: On your phone, open Microsoft Authenticator and tap the “Add account” (“+”) button in the upper-right. Then, tap “Personal account.” You will be prompted to “Scan QR code” or “Sign in with Microsoft.” The former is easier, but that uses the same process described in the previous article. So tap “Sign in with Microsoft” instead.
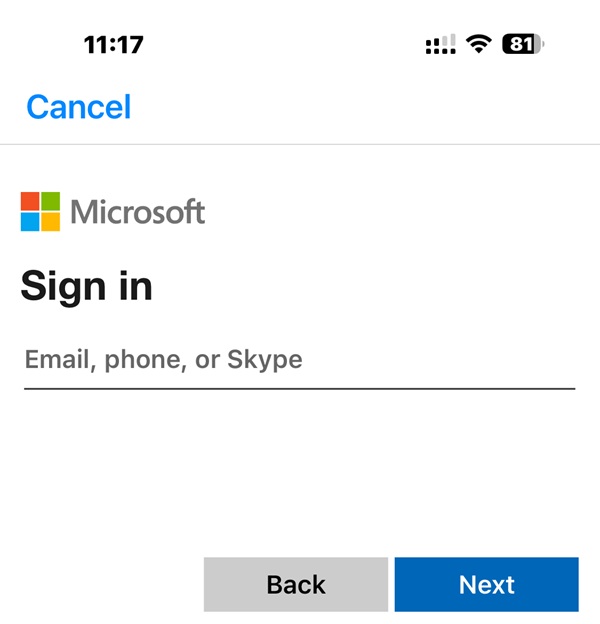
Enter your MSA email address as prompted and then tap “Next.” Then, enter your password as prompted. If you previously configured two-step verification as I recommend, you will also have to complete that process, perhaps by entering a code that’s sent to an alternative/recovery email account.
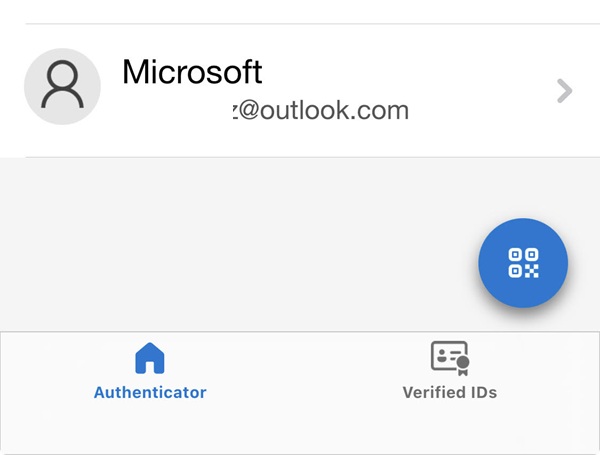
After that, you can see the new account in the list of accounts displayed on the main page of the Microsoft Authenticator app. Note that (most of) these accounts do not display codes like other authenticator apps. That’s because of the more seamless passwordless experience this app provides for MSAs.
To test this experience, open an Incognito or similar web browser window on your PC, navigate to outlook.com, and click the “Sign in” button. In the Sign in screen, enter the email address of the MSA you just added to the Microsoft Authenticator app and click “Next.” You will be prompted to get a code.
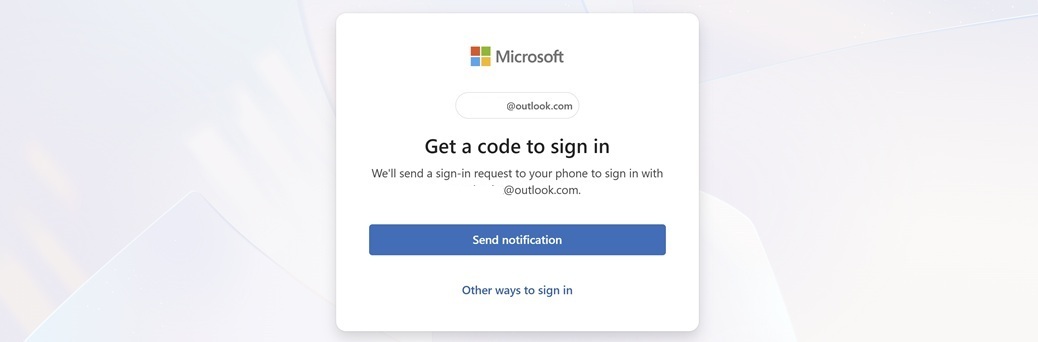
When you click the “Send notification” button, two things will happen nearly simultaneously:
1 – The outlook.com site will display a “Check your Authenticator app” screen with a number.
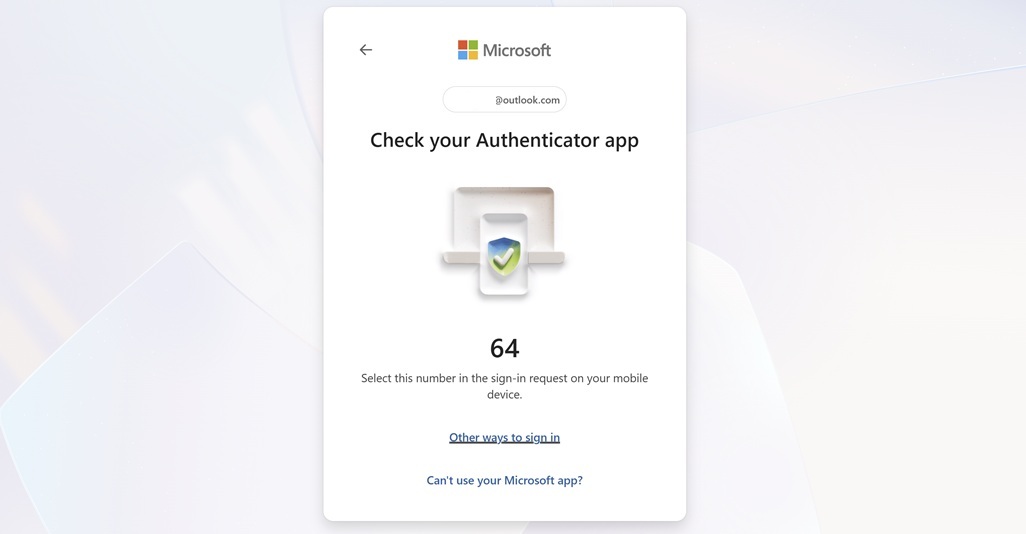
2 – A Microsoft Authenticator app notification will appear on your phone.
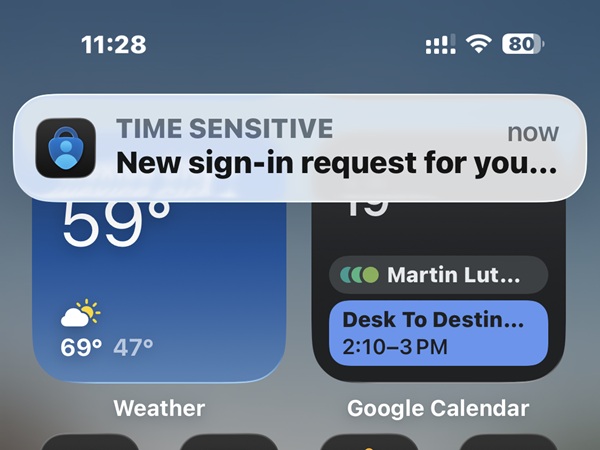
When you tap the notification (or just open the app), it will display a Microsoft Authenticator “Approve sign-in?” screen.
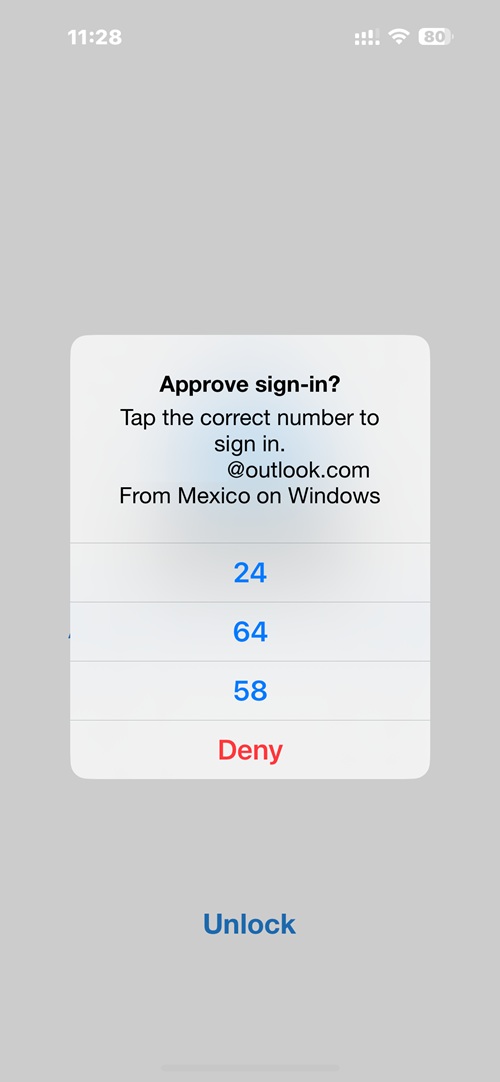
Tap the number displayed on your PC to complete the process. That’s it! You’ll be signed in to outlook.com on your PC.
Well. That’s almost it.
Why this is secure
Your authenticator app(s) are configured to require biometric authentication each time you open them on your phone. This is the default, and when you authenticate using Proton Authenticator, Microsoft Authenticator, or whatever authenticator app on your phone, you will undergo a Face ID or similar authentication process each time. So in addition to picking up your phone and accessing the app, you will use facial or fingerprint recognition (or a PIN) to prove you are you.
More soon.
Gain unlimited access to Premium articles.
With technology shaping our everyday lives, how could we not dig deeper?
Thurrott Premium delivers an honest and thorough perspective about the technologies we use and rely on everyday. Discover deeper content as a Premium member.